CRITICALSTART has introduced a channel strategy for its managed detection and response (MDR) solution that puts partners on an equal footing with the company’s own salespeople.
Under newly enacted rules of engagement, the security vendor’s reseller partners will share a common deal registration system with its field sales team when pursuing sales involving outsourced SOC services.
“Just as any partner would have to do out there, a traditional CRITICALSTART sales rep is going to have to go in and submit a deal registration for MDR opportunities,” says Dwayne Myers, the company’s vice president of channels and alliances. “For all intents and purposes, they are going to be acting as if they were another VAR or reseller.”
The new policy applies to deals involving CRITICALSTART’s MDR service. The company offers assessments and professional services as well, mostly to large businesses, and resells security products from Palo Alto, Cylance, and Forescout, among others.
According to Myers, giving partners first dibs at MDR deals is one step in a larger effort to build a channel capable of helping the company grow market share swiftly. Other steps include the recent introduction of a formal partner program with market developments funds and the rollout last week of a new partner portal.
“We’ve made a conscientious decision to really try to get our MDR offering out to as many customers as possible as quickly as possible,” Myers says. “Trying to do that on a national level required us building out a channel model and going to market with channel partners.”
Myers himself, who became CRITICALSTART’s first-ever channel chief in August after a stint most recently at Palo Alto, is part of that partner recruitment drive. Other milestones include U.S. distribution agreements with Ingram Micro in July and SYNNEX the following month. The company is negotiating alliances with additional distributors, in North America and elsewhere, that Myers declined to identify.
According to Myers, having a channel sales program will help CRITICALSTART align its go-to-market efforts more easily with key partners in the vendor community. “All of these organizations have channel programs as well,” he notes. “We are now able to go in and work very closely with their field sales teams.”
Founded in 2012, CRITICALSTART created its MDR service a few years later. Most SOC outsourcers, according to Myers, are too overwhelmed by input from customers to inspect more than the most suspicious events. “This was inefficient, and so CRITICALSTART decided to flip the model on its head,” he says. “We look at every event that comes in as untrusted events until we can verify exactly what it is.”
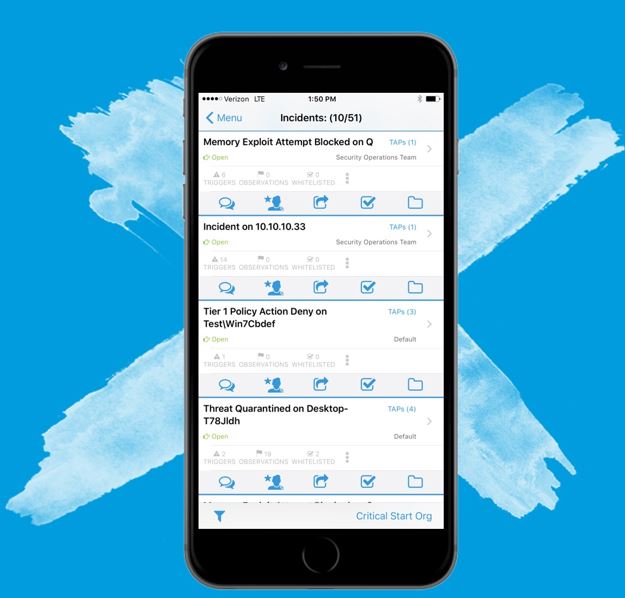
If the company’s software recognizes an event, it automatically executes mitigation best practices defined earlier in a corresponding “runbook.” If the threat is a new one, the system forwards information about it to a security analyst. The company alerts end users about serious issues and applies remediation measures, either on behalf of the customer or in conjunction with them. “We can communicate with them via their mobile app, where they have full access to see exactly what our analysts are seeing, communicate back and forth with them, and take action,” Myers says.
Whether serious or not, all events appear in a ledger that customers can view at any time. “We’re providing full transparency,” Myers says. “Our customers can see exactly what logic was applied to every single alert that comes in.” At the conclusion of the assessment and response process, analysts create a new runbook to automate future appearances of the threat.
According to Myers, the emphasis on automation in CRITICALSTART’s methodology allows the company to do work that might occupy 100 analysts at other vendors with just 20 instead, and charge less as well. “We’re actually less expensive because we have less operational overhead,” he says.
CRITICALSTART’s end user customers range in size from Fortune 500 businesses to companies with around 75 employees. Most of those organizations have at least some in-house security professionals on staff.
To further accelerate channel-building efforts, Myers recently hired regional channel managers for the eastern, central, and western U.S. Identifying promising recruitment candidates in consultation with key vendors will be among their early priorities. “We’re going to be working with them to identify key partners in those geographies for those manufacturers that they already have good relationships with,” Myers says.
At present, he continues, CRITICALSTART has seven partners in all. Talks are underway with another 15 to 20, and the company hopes to have roughly 50 resellers, ranging in size from national brands to regional players to smaller companies, by this time next year.
“We’re growing this out rapidly,” Myers says.
Outsourced services for channel pros without security expertise are steadily proliferating. SolarWinds MSP, for example, introduced threat monitoring services in collaboration with third-party specialists a little over a year ago, which was roughly three months after Continuum formally launched a SOC service of its own. Acronis, for its part, announced multiple outsourced services in August and Sophos launched a managed threat response service last week.