Datto and security vendor Huntress Labs have foiled a hacker’s attempt to sell administrative credentials stolen from an undisclosed MSP based in the eastern U.S.
In an incident that unfolded across the closing months of 2019, an attacker posted an offer on the dark web to sell access to a control panel used by the MSP to manage servers for approximately 20 clients, including law firms, accounting practices, and a pharmaceutical company.
The successful effort to identify the targeted MSP, warn them of the theft, and help them mitigate the impact involved critical assistance from ConnectWise. Huntress CEO Kyle Hanslovan discussed those efforts with ChannelPro during ConnectWise’s IT Nation Connect event last October in Orlando, but requested confidentiality to protect the MSP and their end users until remediation was complete.
“Security is one of those things that if you get it wrong and tip the hacker off, we can make it way worse for an MSP, and there’s no reason to do that,” Hanslovan said last year.†
Actions to protect the MSP and investigate the hacker were coordinated through an MSP information sharing and analysis center (MSP-ISAC) quietly formed by Datto, Huntress, ConnectWise, and Kaseya last summer, and since joined by numerous other vendors who exchange threat information through a Slack channel.†
“Threat-sharing is super critical,” Hanslovan told ChannelPro last year. “If MSPs don’t get behind their own, we’re not going to progress.”
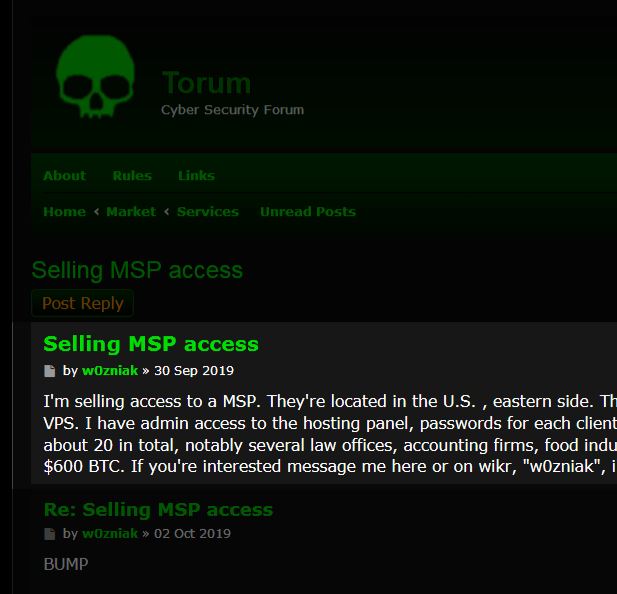
The story publicly disclosed today began last October, when Datto employees performing a routine dark web scan spotted a post by someone claiming to have successfully gained administrative access to a control panel used by an unidentified MSP to manage virtual private servers for its clients. Passwords for each of those clients, the post said, could be acquired through the management console as well. The hacker, identified as “w0zniak”, offered to sell the stolen credentials for $600 in Bitcoins.
Datto brought the discovery to the MSP-ISAC, and Huntress soon began efforts to determine who the compromised MSP was and acquire intelligence about the attacker. Using an assumed identity, the vendor offered to pay $500 in Bitcoin for information on how w0zniak got access to the MSP’s control panel.
“I’d want proof of access (screenshots), learn how you got in, (phishing, RCE, RDP), customer list, proof of number of computers, list of compromised user accounts,” the Huntress message said.
“I was able to get in via phishing the credentials,” the hacker replied. “User accounts, customer list, and compromised accounts I can show via screenshots…MSP is a great target because of the plethora of clients.”
The attacker did subsequently provide screenshots of the stolen panel. Clues in those images helped Huntress identify the victimized MSP. Additional hints suggested that they were a ConnectWise partner. Concerned that the MSP would be unlikely to believe a security warning from a vendor they hadn’t worked with before, the Huntress team approached then ConnectWise Chief Information Security Officer and MSP-ISAC member John Ford, who notified the MSP about the theft.
“Reflecting on this story, it perfectly highlights how close collaboration and threat intel sharing, even between competitive vendors, can be used to go head-to-head against hackers. Putting our egos aside and succeeding at a common goal is something we can all be extremely proud of,” says a Huntress blog post published today.
Ryan Weeks, Datto’s chief information security officer and a charter member of the MSP-ISAC, shared similar thoughts today in a separate blog post. “The key takeaway here is that none of this would have been possible if it weren’t for each individual’s commitment to collaboration. We are proud to be members of the MSP-ISAC community and willing to share our expertise, learn from others, and grow stronger together to combat this endemic threat,” he writes.
The threat is indeed pervasive. According to Huntress, w0zniak put credentials belonging to another MSP with about 100 clients for sale on the dark web just weeks after the first listing.
With hackers increasingly aware that managed service providers possess a wealth of passwords and other valuable information about end users, cybercrime against MSPs and the software vendors who serve them is on the rise. The problem has already attracted the attention of the Department of Homeland Security, which issued a warning about advanced persistent threat activity against MSPs in October 2018.
The federal government has been encouraging businesses to form information sharing and analysis organizations (ISAOs) like the MSP-ISAC since 2015. ConnectWise launched an information sharing group named the Technology Solution Provider-Information Sharing and Analysis Organization (TSP-ISAO) last August. It announced the appointment of an executive director, plus two donations of seed money by company founder Arnie Bellini and an agreement with the University of South Florida to develop an open source information sharing and automated response platform, last fall at IT Nation Connect.