The story of how Datto, Huntress Labs, and ConnectWise blocked the sale of an MSP’s administrative credentials on the dark web, which mostly took place last year but first came to light last week, offers a fascinating glimpse into the world of cybersecurity cloak-and-dagger work.
It also, however, provides a sobering illustration of the perils faced by MSPs now that hackers view them as a convenient way to compromise dozens of end users at once, not to mention the clearest look yet at the quiet effort by a growing body of vendors to counter that threat through cooperative action.
That effort began last summer with a message from Ryan Weeks, Datto’s chief information security officer, to Huntress Labs CEO Kyle Hanslovan and Vice President of ThreatOps John Ferrell. Inspired by a webinar in which the Huntress executives urged their peers to join forces in the fight against cybercrime, Weeks reached out to offer his support. Within days, the two companies met and formed what’s since become the MSP-ISAC, a security information sharing and analysis center (ISAC) for the managed services community.
“It started out this MSP-ISAC was just nothing more than a Slack channel for Datto and Huntress to communicate,” recalls Hanslovan.
Those vendors soon invited ConnectWise and Kaseya to participate as well, and other firms later joined them. Today, the MSP-ISAC has over 30 members, and grassroots recruiting continues. “Nights and weekends, we’re inviting security people from other channel companies through LinkedIn or through our direct relationships to join,” says Weeks.
The overarching goal, he continues, is to even the odds against attackers by exchanging best practices and pooling threat information that would otherwise reside in siloes across the industry. In particular, Weeks hopes to make the group a source of insights on what security experts call “TTPs,” the tactics, techniques, and procedures that bad actors use to break into targeted systems. That’s information rarely disseminated beyond cybersecurity experts at present.
“I want it to be a community where actionable information is presented that can help MSPs adapt their security programs,” Weeks explains, noting that the ISAC concept has a long history in other industries. “This model is proven,” he says. “It’s worked really well in healthcare, in financial services, and so it’s not that this is a new or groundbreaking idea.”
Sadly, much about the breach disclosed last week, in which a hacker put passwords belonging to an MSP in the eastern U.S. for sale on the dark web, is familiar too. Datto is one of many vendors that monitors the cybercrime underworld for signs that one of its partners, or an end user supported by those partners, has been breached, and then proactively contacts anyone it believes to be in danger.
“We do a lot of that on a weekly, monthly basis,” Weeks says.
The threat that Datto stumbled across last October, however, was unusual. Normally, Hanslovan says, thieves with stolen cyber-goods to sell operate in the deepest recesses of the dark web. This new for-sale listing, by contrast, was comparatively out in the open, on a site called Torum. It also made starkly real what for most MSPs remains an abstract phenomenon—the ongoing increase in threat activity against their business systems.
“Here’s an MSP for sale, like you’re having a yard sale or something,” Hanslovan says of the discovery. “It blew my mind.”
Datto, Huntress, and ConnectWise hoped that publicizing the incident, after properly ensuring the victim and its clients were safe, would similarly grab the attention of MSPs, and clarify the risks they now face. There’s a lot of fear, uncertainty, and doubt about those risks at present, according to Weeks.
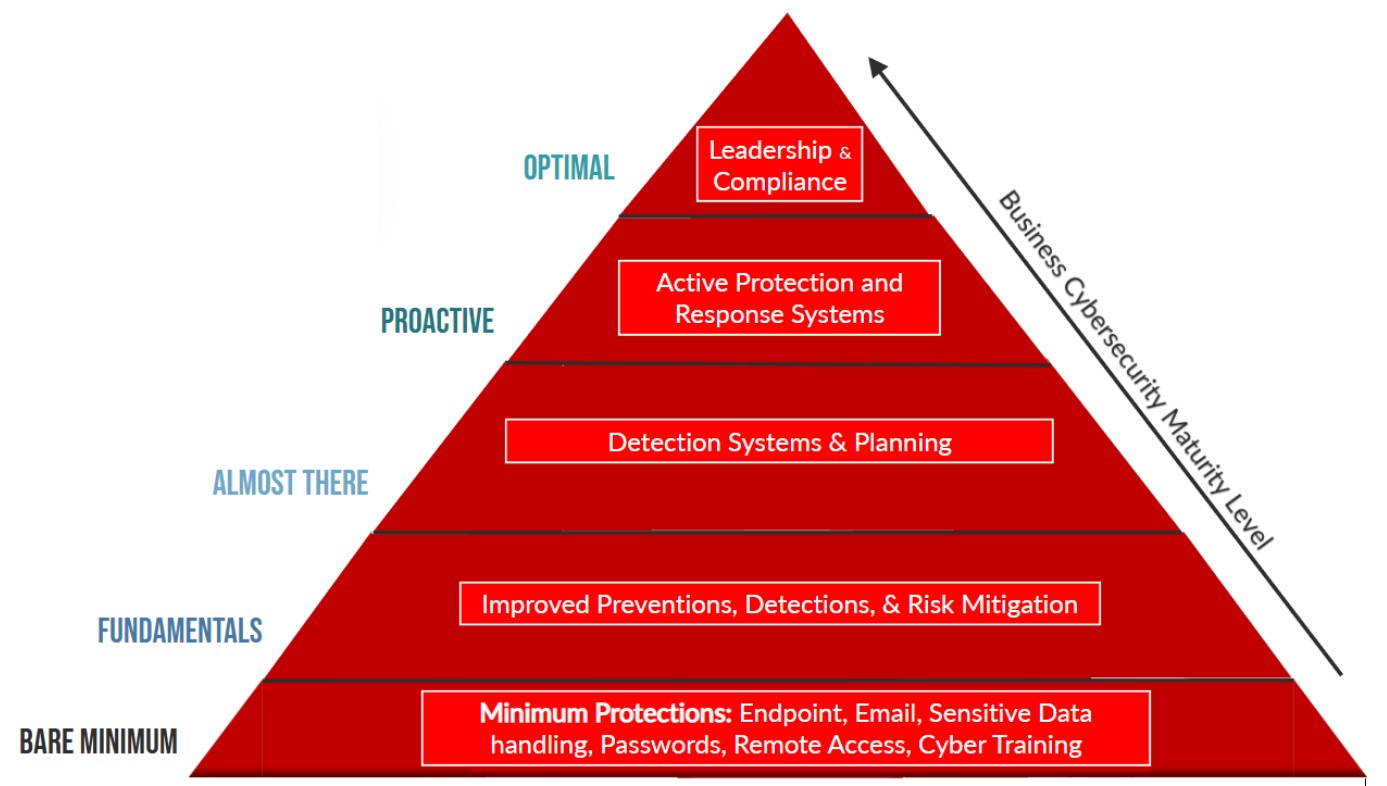
“Usually, a lack of understanding is what breeds fear, and so our main goal with sharing this information was to make this a little bit more accessible and give them a little bit more insight into how these attackers are doing what they’re doing and why they’re doing it, so that [MSPs] can begin to understand a little bit better this ecosystem, and maybe leverage some of that insight to figure out how they want to prioritize improvements to their own security programs,” he says.
Or to put it more bluntly, according to Hanslovan, few people growing up truly appreciate why they shouldn’t touch a hot stove until they get burnt. “Somebody here got burnt,” he says. “We were going to give that victim some time to clean up, but we felt it was imperative to educate the community.”
There are plenty of potential lessons in this story to learn from, Hanslovan adds. The attacker claims to have used phishing to gain entry to the target MSP’s software, for example. That means better security awareness training might have prevented the breach from happening, and two-factor authentication could have kept it from mattering.
Weeks had a second motivation for calling attention to the hack. “If I’m being super honest, my hope is that other security vendors in the channel space with capable, qualified security teams will want to join this community and work with us to continue to try and keep MSPs safe,” he says.
There’s no shortage of issues for the fledgling group to think its way through, from funding and staffing itself to enhancing its effectiveness against newly found threats. The work Huntress did to block this recent attack is impressive but not scalable, Weeks observes.†
There are thornier topics to ponder as well, Hanslovan notes, like when and how to pull law enforcement agencies into an investigation, and how to disseminate threat information without making bad situations worse. What, for example, if someone in the group exposes information about a breach before the attacker’s identity has been verified, or the victim has been shielded from harm? What if someone in the organization takes vigilante action against a hacker?
“It’s not just about growing and making sure people can collaborate, it’s making sure we’re doing this responsibly,” Hanslovan says.
Weeks wants to make further progress on matters like that before opening the MSP-ISAC’s doors widely. “I believe that it needs to start with the vendor community, and then once we really get really moving with this, then we figure out how to expand this knowledge out to MSPs,” he explains.†
That said, MSPs impatient to join the group now can email ciso@datto.com or kyle@huntress.com. There’s certainly more than enough work to go around. Within just the past few weeks, MSP-ISAC members have spotted multiple dark web posts from a new attacker claiming to have penetrated an MSP management system that oversees 86 “active hosts,” which could mean 86 servers across multiple end users or a single end user with 86 compromised devices.
“You really don’t know until you really start learning more about the hacker,” Hanslovan says. There will be plenty more hackers to research in the coming months and years, he warns.
“This is not a one and done,” Hanslovan says. “This is just the beginning.”