Kaseya hopes to bring the cloud version of its VSA remote monitoring and management solution back online on July 6th, and to distribute a patch for the on-premises version within the ensuing 24 hours, according to the latest update on the company’s website.
That timing is subject to revision as the IT management vendor completes testing and validation of the updated software. Kaseya’s executive committee will make a final decision about restoring service between 8:00 a.m. and noon Eastern Daylight Time on Tuesday. If it chooses to proceed, the software-as-a-service platform will come online between 2:00 p.m. and 5:00 p.m. E.D.T.
Kaseya had hoped to begin restoring service for users outside North America as early as 4:00 a.m. E.D.T. on July 5th, per previous guidance. Early that morning, Kaseya’s website says, the vendor’s executive committee opted to delay that process “to best minimize customer risk.”
VSA was struck Friday by an “incredibly sophisticated” attack, in the words of Kaseya CEO Fred Voccola during a conversation with ChannelPro yesterday. The online version of that product has been offline since then, and the company continues to urge users of the onsite version to keep the software offline as well.
To date, the company says, fewer than 60 MSPs have been infected by the incident, and there have been no new reports of compromised MSPs since Saturday.
A Compromise Detection Tool has been available since Friday, and has been downloaded by over 2,000 users so far. The latest version of that tool searches for indicators of compromise, evidence of data encryption, and a ransom note from the attacker, which according to the FBI is the REvil ransomware consortium.
REvil has demanded a $70 million ransom to decrypt all impacted end user data, according to Reuters on Monday. “I can’t comment ‘yes,’ ‘no,’ or ‘maybe’,” said Voccola to Reuters when asked about meeting the ransom demand, or accepting REvil’s offer to negotiate it. “No comment on anything to do with negotiating with terrorists in any way.”
Voccola similarly declined to tell ChannelPro yesterday whether or not Kaseya has been contacted directly by REvil.
Kaseya believes that between 800 and 1,500 downstream end users, out of the approximately 800,000 to 1,000,000 mostly small and midsize businesses supported by VSA customers, have been victimized, per a press release issued Monday night. Perpetrators of the attack exploited privileged access rights to those companies in VSA to distribute ransomware to them.
According to Voccola yesterday, Kaseya is helping those organizations, either directly or through their MSP, recover from the strike.
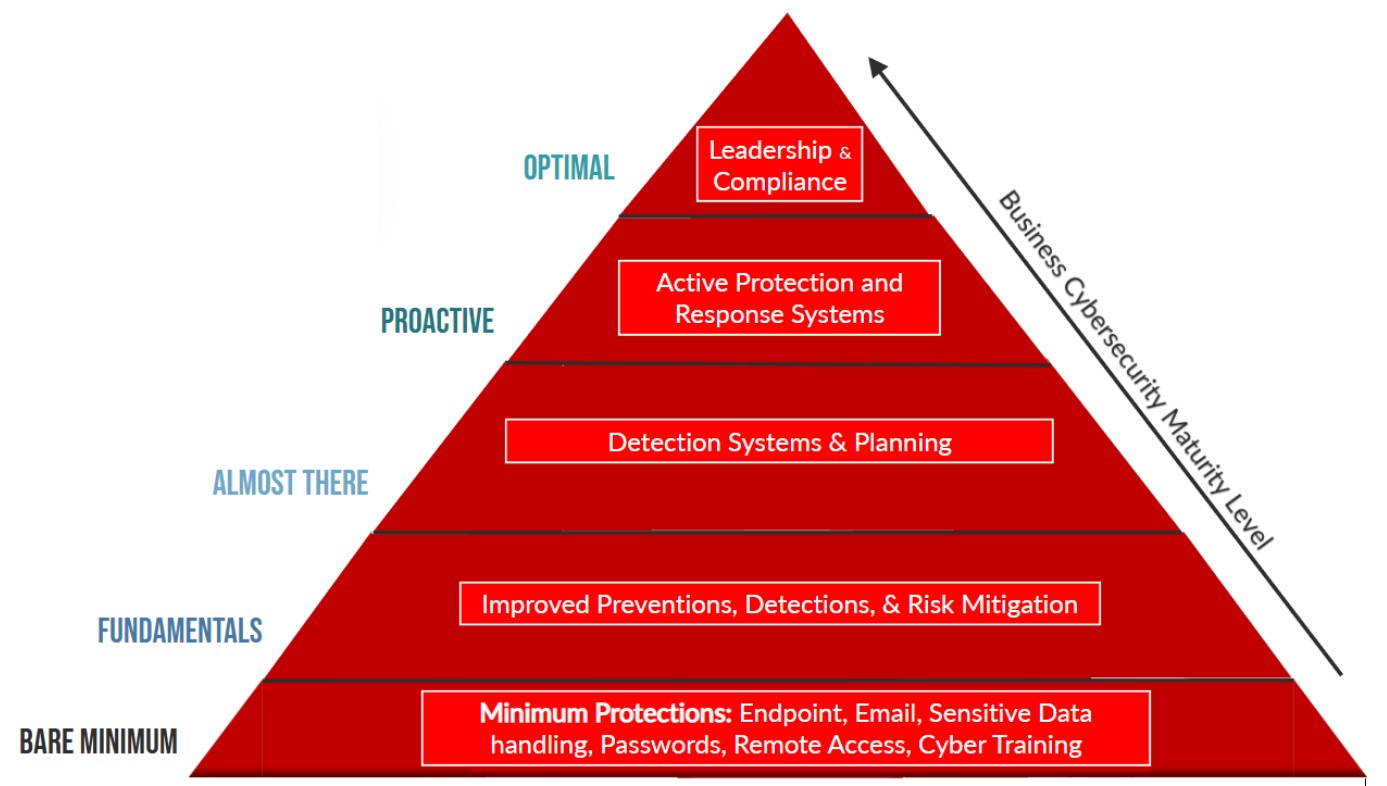
Users may be required to implement additional security measures recommended by the FBI and the Cybersecurity and Infrastructure Security Agency (CISA) before using the updated SaaS or on-premises version of VSA, according to the latest web statement.
“Kaseya met with the FBI/CISA tonight to discuss systems and network hardening requirements prior to service restoration for both SaaS and on-premises customers,” the company says. “A set of requirements will be posted prior to service restart to give our customers time to put these counter measures in place in anticipation of a return to service on July 6th.”
VSA, Kaseya says, is the only one of the 27 modules in the company’s IT Complete product suite affected by the REvil breach. Other modules include BMS, Kaseya PSA solution, the IT Glue documentation platform, and the Unitrends BDR portfolio.
Kaseya acquired managed SOC service provider RocketCyber in February. That unit’s leaders and analysts, according to Voccola, have been “super helpful” in diagnosing and addressing the REvil assault.
Kaseya identified the root cause of the VSA breach within hours of the attack, but won’t disclose details until cleared to do so by the federal government, which is conducting a criminal investigation at present.