IF YOU LIKE THINGS TRIED, true, and familiar, our annual Vendors on the Vanguard list may not be for you. If, on the other hand, you’re open to partnering with anyone who can help you make more or spend less, check out our latest crop of lesser-known, up-and-coming, and underappreciated software and service providers.
SECURITY
Coronet
Securing clients working from home due to the coronavirus pandemic has been a challenge for most channel pros recently. It’s likely to remain a challenge even after stay-at-home restrictions ease, as businesses grown used to telecommuting embrace it as a way to save money on office space and boost employee satisfaction.
Coronet‘s SecureCloud platform is an unusually comprehensive option for protecting SMB workforces at home and the office. The system includes endpoint and Wi-Fi security; Office 365, Google G Suite, Dropbox, Box, Slack, and Salesforce protection; data loss prevention technology; and even cyber insurance in one big package that sells for as little as $5.99 per user per month. An MSP partner program has been available for the last year too. coro.net
Dark Cubed
Vince Crisler knows plenty about security, enough to get hired as chief information security officer during the George W. Bush administration. The company he co-founded after that experience, Dark Cubed, is designed to make the considerable expertise of people like himself both easy enough for channel pros to consume and inexpensive enough for them to afford.
Equipped with an interface that the company says most users can figure out in minutes, Dark Cubed’s platform automatically imports and analyzes firewall log data, and assigns each connection a simple risk score. Users receive alerts when the system detects threats, along with remediation advice that even people without hard-core security training can execute. Users can also block and unblock traffic sources or services with a single click, or enable automatic blocking of especially risky connections. darkcubed.com
SaaSAlerts
If your client’s CEO is using Office 365 from an IP address in San Francisco and Salesforce from one in Boston at the same time, she’s either got magical powers over time and space or is being hacked. Assuming the latter is true, only a cross-platform cloud security tool like SaaSAlerts will warn you about the problem.
Introduced last month, SaaSAlerts continuously monitors Office 365, Salesforce, Google G Suite, Dropbox, Box, and Slack for signs of data theft, data vulnerability, and malicious activity, correlating abnormal patterns (like someone working in two different applications from two different locations simultaneously) along the way. If it spots trouble, the system issues an alert and opens a ticket in ConnectWise Manage or Datto’s Autotask PSA.
Pricing starts at 45 cents per user per month on a one-year contract with a $100-a-month minimum. More flexible month-to-month rates go for 50 cents per user. To help MSPs protect clients during the COVID-19 crisis, the product is available free of charge through September 1 to the first 500 companies that subscribe. saasalerts.com
OPERATIONS AND MANAGEMENT
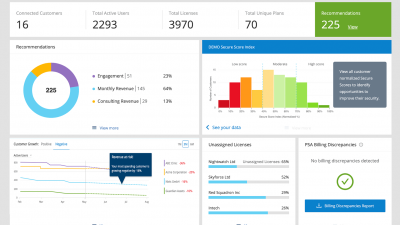
Accordo
Numerous vendors make products that businesses can use to optimize Office 365 spending. Accordo‘s solution, though, includes additional features cloud service providers will appreciate, such as a dashboard that shows aggregated Microsoft Secure Score data from all your accounts, a “”Growth Widget”” that calls your attention to rises and dips in end-user license consumption, and a tool that finds discrepancies between billing data in Microsoft’s administration console and corresponding figures in ConnectWise Manage or (starting soon) Datto’s Autotask PSA.
Pricing for the system, which is available exclusively through the channel, runs a flat $200 a month for the first 200 active Office 365 users you support and then 30 cents or less monthly for additional seats, depending on volume. The partner program includes dedicated account management. accordo.com
Concertium
If you’re like most MSPs, you have plenty of visibility into endpoints, cloud licenses, service tickets, and everything else you work on all day. Your customers, on the other hand, don’t. That’s a problem for anyone who serves—or someday wishes to serve—companies large enough to have their own IT department.
Captain’s Chair IT (CCIT) from Concertium aims to give midsize businesses and “”co-managed IT”” clients the same end-to-end business intelligence that their MSP enjoys through a single pane of glass, offering data on everything from hardware and software assets under management to ticket and device status, application performance, and website analytics, plus pending quotes, ongoing projects, and roadmaps agreed to during quarterly business reviews. An MSP itself, Concertium originally developed CCIT for in-house use, and gives the system substantial credit for enabling two straight years of 40% growth. concertium.com/captainschair
Mission Control
Saying you offer 24/7 support is easy. Delivering something more meaningful than a sleepy “”we’ll look into it”” when a call arrives at 2 a.m. on a Sunday is a little harder. MSPs looking for overnight and weekend assistance with NOC and help desk duties should include Mission Control in their evaluation process.
The company has no contracts, minimums, or onboarding fees, and serves North American users exclusively through North American technicians, with no overflow or after-hours outsourcing to third parties or subcontractors. Strategic partners include Datto, Auvik, IT Glue, and SolarWinds Passportal. Technologies supported include systems from Cisco Meraki, Dell, HP, Microsoft, SonicWall, Sophos, Veeam, VMware, and Webroot. The company sells only to channel pros, so client poaching isn’t an issue. missioncontrolnoc.com
TimeZest
Calendly for ConnectWise. If you’re familiar with Calendly, the online appointment scheduling solution, those three words are all you need to know about TimeZest. Launched last year, the system lets end users book technician appointments for help with support issues on a self-serve basis.
Drawing on tight integration with the ConnectWise Manage PSA platform, TimeZest automatically emails a link that recipients can use to schedule service calls whenever a technician opens a help desk ticket requiring follow-up. When an appointment is booked, the system automatically reserves time on the technician’s calendar, updates the associated ticket, and sends the customer a second email they can use to place a meeting on their own calendar.
ConnectWise found the whole thing so ingenious that it awarded TimeZest first place in its annual Pitch IT contest for startup creators of software that extends the capabilities of the ConnectWise managed services suite. timezest.com
Zomentum
Admit it: Sales isn’t your favorite activity. It’s also probably not your easiest if you’re using a series of tools for managing opportunities, building proposals, and collecting signatures. Zomentum‘s solution, which entered general availability late last year, combines all those functions into a single package that’s specifically tailored to the needs of MSPs and integrated with PSA software from ConnectWise, Datto, and Kaseya. Two-user subscriptions that you can cancel anytime sell for $99 per month (plus another $29 a month each for additional users) and include free onboarding and support. zomentum.com
INTERNET OF THINGS
ReFirm Labs
Sensors, cameras, and other Internet of Things devices are powerful, plentiful, and dangerously difficult to secure, mostly because the tools you use to manage traditional endpoints rely on agents, which few IoT gadgets can accommodate.
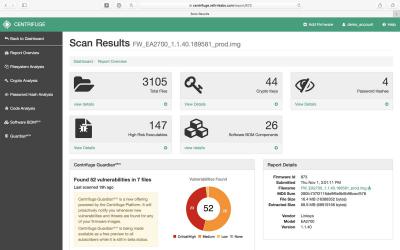
The Centrifuge Platform from ReFirm Labs is an exception to that rule, however. Give it an image of an IoT device’s firmware and the cloud-based system will automatically evaluate the security of that code, suggest fixes to any vulnerabilities it finds, and continuously warn you of new threats. Created by a team of former NSA cybersecurity operators, Centrifuge detects potential zero-day vulnerabilities, hidden crypto keys, backdoor passwords, and known vulnerabilities in IoT devices without help from agents or access to source code. APIs make integration with third-party management tools possible too. refirmlabs.com
STORAGE AND DATA MANAGEMENT
Blancco Technology Group
Privacy regulations are often every bit as prescriptive about how data is deleted as they are about how it’s stored. Blancco Drive Eraser turns deletion into an easy one-click process, its manufacturer says, while also documenting everything it erases, so channel pros and their clients can prove they disposed of data responsibly should auditors come calling. Better yet, Blancco asserts, MSPs can turn the solution into a source of recurring “”erasure-as-a-service”” revenue from security-conscious businesses with lots of hard drives to cleanse. Small business bundles that include a year of Level 2 support and an hour of training make the product an affordable option for companies with more modest needs too. blancco.com
Egnyte
Whether large or small, your customers have lots of files in on-premises storage systems and cloud solutions like Office 365 and Google G Suite. How much do they—or you—know about what’s in all those documents? Egnyte Protect is a content governance solution designed to help businesses find sensitive information and then ensure that it’s used and stored appropriately. Companies can restrict access to specific people, keep files confined to white-listed locations, enforce compliance with regulations like HIPAA or PCI DSS, and more. If someone attempts to break those rules or otherwise behaves suspiciously, moreover, the system will tip you off promptly. egnyte.com
Files.com
Once a great new innovation, cloud storage isn’t all that impressive anymore, is it? Smart cloud storage of the kind Files.com is designed to support can be, however. Equipped with APIs, an SDK, and drag-and-drop development tools simple enough for nondevelopers to use, the system is less an online data repository than a foundation for workflow automation solutions that collect information from multiple sources and feed it back out to third-party applications. The power company serving Las Vegas, for example, uses Files.com to consolidate readings from smart meters across the city, export it to a billing application, and then archive it for future reference.
Both per-user and flat-rate subscriptions are available at prices that, according to Files.com, leave room for up to 35% margins. files.com
SalvageData
Backup software is essential. Backup failures are inevitable. When a customer calls you about accidentally deleted files or corrupted drives on a device they never told you about, or you make the painful discovery that a backup you never tested is unusable, SalvageData could be a handy source of emergency help.
Send the company a PC, hard drive, RAID array, NAS unit, or other device, and they’ll send you a quote and turnaround estimate. Both the evaluation and inbound shipping are free. Give them the green light to proceed, and they’ll copy everything recoverable to brand-new external storage media or make it available for download. A “”no recovery, no charge”” policy ensures that you pay nothing if they can’t get your data back. salvagedata.com
COMMUNICATION AND COLLABORATION
VisibilityOne
COVID-19 will be gone someday soon, we hope. Remote work and videoconferencing, however, are here to stay, which means managing unified communications and collaboration products from Zoom, Cisco, Poly, Logitech, and others through a host of management tools is the SMB channel’s latest headache. VisibilityOne’s patented UCC management solution, which debuted last year, seeks to replace those separate interfaces with a consolidated dashboard for administering all the devices, applications, and operating environments your customers utilize in one place. A white-label solution that you can attach your own brand to, the system comes in a multitenant edition specifically for MSPs. visibility.one
MOBILITY
Charles River Consultants
Like you and everyone else these days, your customers communicate via SMS, voice, email, and fax through multiple tools and apps on often personally owned devices. Charles River Communications from Charles River Consultants pulls all that activity together into one system that’s not only easier to use than multiple platforms but safely segregated from personal data as well. That’s functionality much appreciated by users in regulated industries like healthcare and financial services, as well as people in fields like real estate (and managed services) who hate receiving work-related messages in the same apps they use to communicate with family and friends. www.crc.net
Cubed Mobile
Like Charles River Communications, Cubed Mobile’s solution is for users who combine business and leisure on the same smartphone. But while the former system focuses on messaging, the latter containerizes everything you do with a phone in a totally isolated, centrally managed virtual device-within-a-device. The result is one piece of hardware that performs two entirely different functions securely and without swapping SIM cards.
Technicians can also use the management tool to wipe business data off the phone of someone leaving the company, or draw on the backup feature to transfer a user’s entire virtual workspace from a lost or stolen device to its replacement. cubedmobile.com
Image: iStock