Cybersecurity Awareness for New Hires
In this article, you will learn:
- Why new hires are prime targets for zero-day social engineering attacks
- How onboarding gaps create measurable risk for SMB clients
- A four-point checklist MSPs can give hiring managers immediately
- Practical ways to integrate onboarding security into managed services
Cyber Aware from Day 1
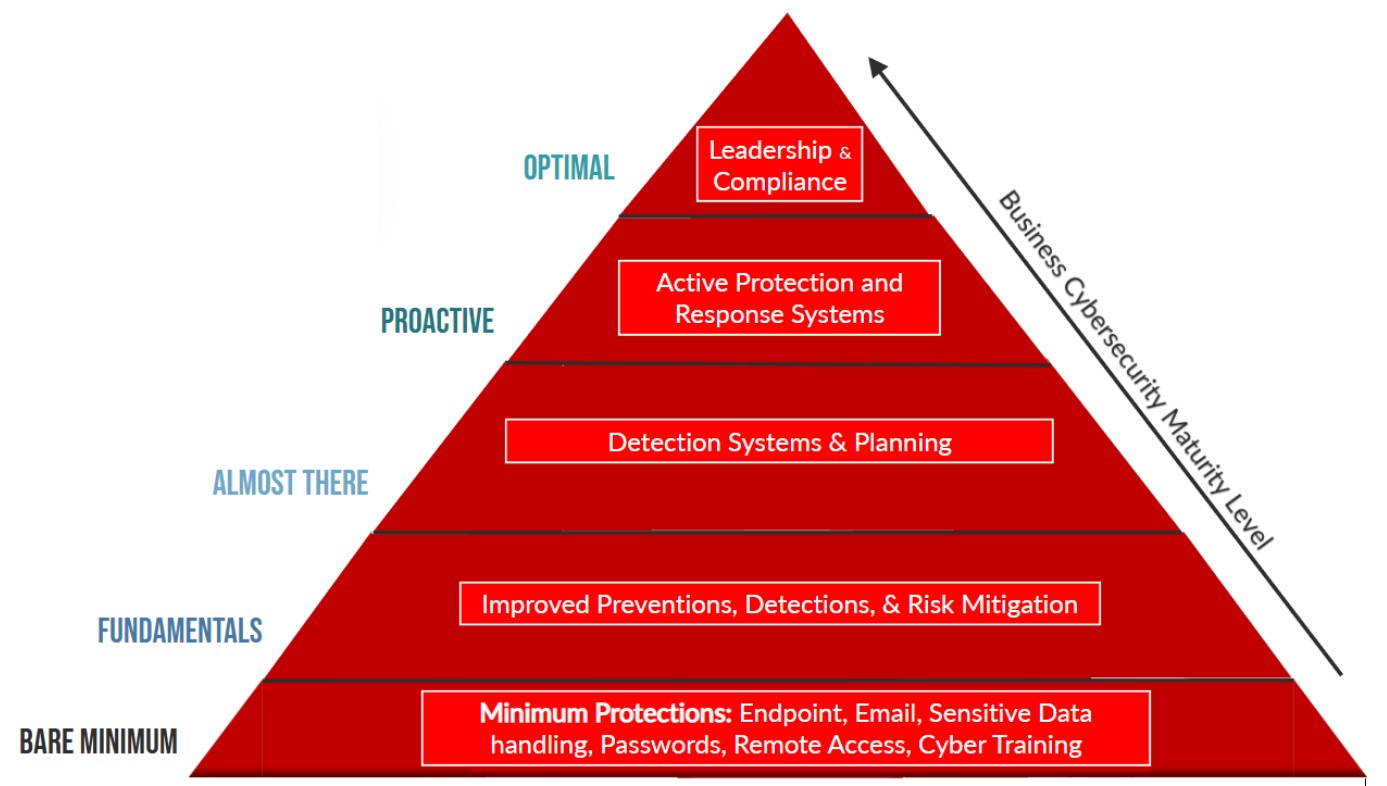
Most MSPs have strengthened phishing protection, MFA enforcement, and endpoint security across their client base. However, the first day for a client’s new hire is a vulnerability that often goes unaddressed.
Cybersecurity awareness cannot begin after trust is assumed. For MSPs serving SMB clients, protecting new employees from zero-day cyber scams is a practical, preventative step that aligns people, process, and technology.
The Tale of the Onboarding Scam
A recent incident involving a small business illustrates this point. A new employee, eager to make a strong first impression, received a message that appeared to come from the company owner. The message welcomed them and asked for a favor. “Purchase gift cards for the team as a surprise and please keep it confidential.” This was meant to be a surprise and reward for the entire team.
The new and gracious employee complied. After buying the cards, they were asked to scratch off the backs and send the codes electronically. At that moment, something felt off. They paused and decided to take the risk to verify internally.
The message was fraudulent.
The attacker had monitored social media, identified the employee’s public job announcement, and timed the impersonation perfectly. The individual had not yet learned internal communication norms or verification procedures. The first day became the attack surface.
How to Protect New Employees from Threat Actors
For MSPs serving small and midsized businesses (SMBs), this is an emerging pattern. Onboarding is predictable and predictability creates opportunity for attackers. Below are four actionable steps MSPs can implement with their clients immediately.
1. Start Cybersecurity Awareness for New Hires Before Day 1
Security awareness training often begins after credentials are issued. That leaves a window between offer acceptance and operational integration.
MSPs should encourage clients to send a brief pre-boarding cybersecurity message before the employee’s start date. This communication can clearly outline the following.
- Executives will not request gift cards, wire transfers, or confidential data via text.
- Financial approvals follow documented workflows.
- Unusual requests require verification.
- Which official communication platforms are used internally.
A short pre-start briefing reduces ambiguity. When expectations are defined early, abnormal behavior becomes easier to identify. Embed pre-boarding guidance into managed security services to strengthen the overall phishing defense strategy and reduce business email compromise (BEC) risk.
2. Document Executive Communication Norms
Small businesses often rely on informal leadership communication. While culturally positive, informality can create uncertainty for new hires.

Jared Knisley
MSPs can help clients formalize communication norms in a concise onboarding document that addresses:
- Approved internal communication tools
- Who authorizes financial transactions
- How urgent requests are escalated
- Required verification procedures
New employees do not yet know whether the owner typically sends direct text messages or approves purchases casually. Clear documentation eliminates confusion and reduces the effectiveness of impersonation attempts.
Rather than adding bureaucracy, formalizing norms removes ambiguity, which is the foundation of most social engineering attacks.
3. Address Social Media Exposure During Onboarding
Many employees announce new roles publicly. Cybercriminals monitor these announcements and use them to time targeted attacks. MSPs should advise their clients on incorporating social media awareness into onboarding discussions.
- Public start dates create attack timing signals.
- Posting supervisor names can enable impersonation.
- Privacy settings should be reviewed.
- Attackers routinely conduct open-source research.
This is about awareness. For SMB environments without layered compliance teams, informed employees serve as a primary line of defense.
4. Implement a First-week Verification Rule
The first week of employment presents elevated risk. New hires want to perform, may hesitate to question authority, and lack established communication baselines.
MSPs can recommend a formal policy requiring that any financial or sensitive request during the first week must be verified through a second channel. Examples include:
- Call a published company phone number
- Confirm within an authenticated collaboration platform
- Verify directly with HR or finance
This removes emotional pressure from the employee. Instead of appearing skeptical, they are following documented company policy. A structured verification rule is a simple control with significant risk-reduction impact.
Why This Matters for MSPs
Gift card scams and BEC are persistent threats across SMBs. However, attacker timing has evolved. Onboarding events are now part of the attack surface.
MSPs that incorporate onboarding security into their managed services demonstrate operational maturity and strategic advisory capability. Reviewing onboarding workflows during quarterly business reviews, aligning HR and IT processes, and embedding pre-start cybersecurity guidance strengthens the overall security posture.
Onboarding is often considered an administrative task. In practice, view it as a security control. Treating it as such closes a gap attackers are actively exploiting.
FAQs
Q: Are new hires more vulnerable to phishing and BEC?
Yes. New employees lack communication baselines and may feel pressure to prove themselves, increasing susceptibility to impersonation attacks.
Q: Should MSPs be involved in HR onboarding processes?
MSPs should advise on security components that intersect with identity management, communication tools, and financial controls, even if HR manages the administrative process.
Q: Is pre-boarding cybersecurity training necessary for small businesses?
Even a brief pre-start communication that outlines verification expectations can significantly reduce onboarding-related cyber risk.
Q: Why are gift card scams still effective in SMB environments?
Gift cards are easily transferable and difficult to trace. This makes them attractive for attackers conducting social engineering campaigns.
Q: What is the simplest onboarding security control to implement immediately?
Require verification of all financial or sensitive requests during an employee’s first week.
Dr. Jared Knisley founded Fizen Technology in 2015. Through the years, the company developed a strong reputation for delivering scalable, forward-thinking IT solutions to growing organizations. In 2025, XDuce acquired Fizen, rebranding it as XDuce Managed IT and Cybersecurity. This combined Fizen’s proven expertise with XDuce’s global scale, resources, and innovation engine, delivering enterprise-grade cybersecurity, scalable managed services, and strategic IT leadership.
Featured image: Andrii — stock.adobe.com