Zero-day attacks, by their very nature an unknown defense variable, are a serious cybersecurity threat to organizations of all sizes. These attacks exploit new and unexpected vulnerabilities in software or hardware, meaning security teams are forced to scramble to respond to breaches no one is prepared for.
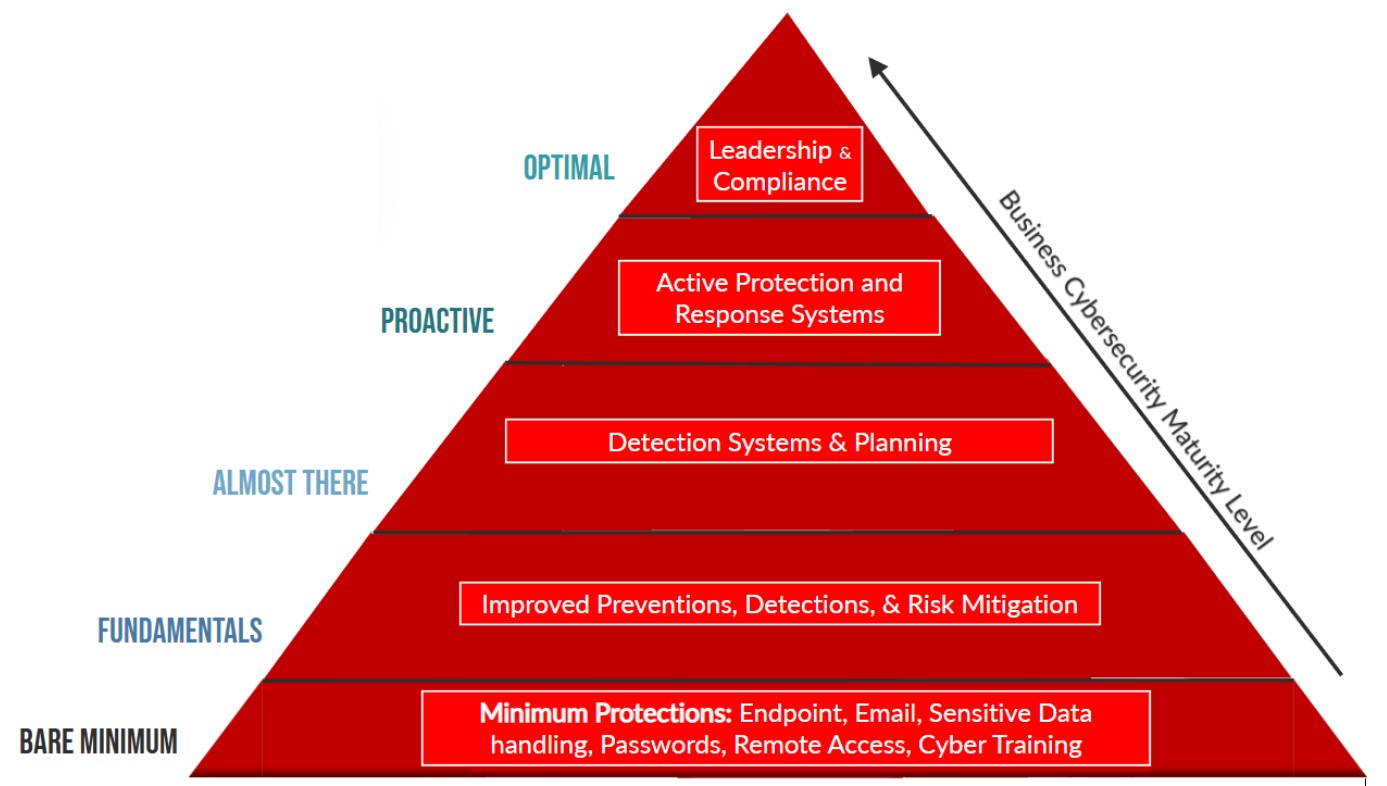
Protecting an organization’s digital assets against such unforeseen threats requires a proactive and layered security approach. It’s not, however, unachievable. Here are six ways to bolster organizational defenses against zero-day threats.
No. 1: A Thorough Patch Management Policy
The first line of defense against zero-day attacks is a rigorous patch management system: ABP, as the acronym goes: Always Be Patching. This requires consistently updating and patching all software and systems. Zero-day attacks target unpatched vulnerabilities, so regular updates close off known security gaps. Utilizing automated patch management tools ensures these updates are promptly applied when released by providers.
No. 2 Adopt Advanced Threat Detection Tools
Zero-day attacks are notoriously difficult to detect using traditional antivirus software—they are, after all, designed to exploit unknown flaws. Advanced threat detection tools that use behavior-based detection techniques rather than signature-based methods are more effective in identifying any suspicious activities. Tools that leverage machine learning and AI can adapt and learn from ongoing network activities, creating a baseline of approved activity and flagging any deviation from ‘normal.’ This helps identify anomalies that could signify zero-day attack activity.

Nik Hewitt
No. 3 Embracing the Principle of Least Privilege
Limiting user access rights within an organization’s network can significantly mitigate the impact of a zero-day attack. By implementing the principle of least privilege, or zero trust, users are granted only the access necessary to perform their job functions. One account may be compromised, but if that account only has access to the data and applications a user needs to do their job, then the attacker’s ability to move throughout an environment is greatly reduced. Regular audits of user permissions and roles ensure that this principle is effectively maintained.
No. 4 Conduct Regular Security Training
Human error is one of the largest security vulnerabilities. Regular training on cybersecurity best practices for all staff members is now a crucial part of the job of any proactive security team. This should include educating employees on how to recognize phishing attempts, the importance of using strong passwords, and the proper handling and reporting of suspicious emails or links. Educating a workforce turns it into a first line of defense, capable of identifying potential threats before they can turn into a breach, in a world where security is everyone’s responsibility.
No. 5 Employ Network Segmentation and Microsegmentation
Network segmentation divides a network into smaller, more manageable, more secure segments, limiting how far an attack can spread. Microsegmentation takes this a step further by creating even smaller (granular) segments at the application or workload level. Embracing microsegmentation tools is rapidly becoming the de facto standard for cybersecurity legislative compliance. This granular approach to network segmentation greatly reduces the attack surface and confines the impact of a zero-day exploit to a smaller, more manageable, isolated portion of a network. This stops bad actors from moving laterally (east-west) throughout environments in the search for privileged accounts.
No. 6 Develop a Comprehensive Incident Response Plan
Despite preventive measures, the possibility of a zero-day attack can’t be entirely ruled out. Therefore, a well-structured incident response plan is essential. This plan should outline the steps to be taken in the event of a breach, including identifying and isolating affected systems, eradicating the threat, and recovering data. Regular drills and simulations of zero-day scenarios ensure that a security team is prepared to respond effectively and efficiently, enhancing their ability to respond if the unthinkable does happen.
As cyber threats continue to evolve, staying ahead of the curve isn’t just a matter of implementing the right tools, but also fostering a culture of cybersecurity awareness and readiness within any organization. Preparation and prevention are always preferable to reaction and remediation.
Nik Hewitt is senior content marketing manager of TrueFort. He specializes in IT and cybersecurity journalism, the company’s brand management, and serves as director of video and audio content.
Image: iStock