Security vendor Huntress has put its managed antivirus solution for Microsoft Defender into general availability.
The new service, which has been in public beta since January, went into full-scale production today alongside new host isolation functionality and the official unveiling of global threat analysis and response capabilities. It’s the vendor’s first prevention-focused offering, and joins a portfolio that already includes threat hunting services, ransomware detection and removal software, and an “external recon” solution that identifies attack surfaces and exposed entry points in a customer’s infrastructure.
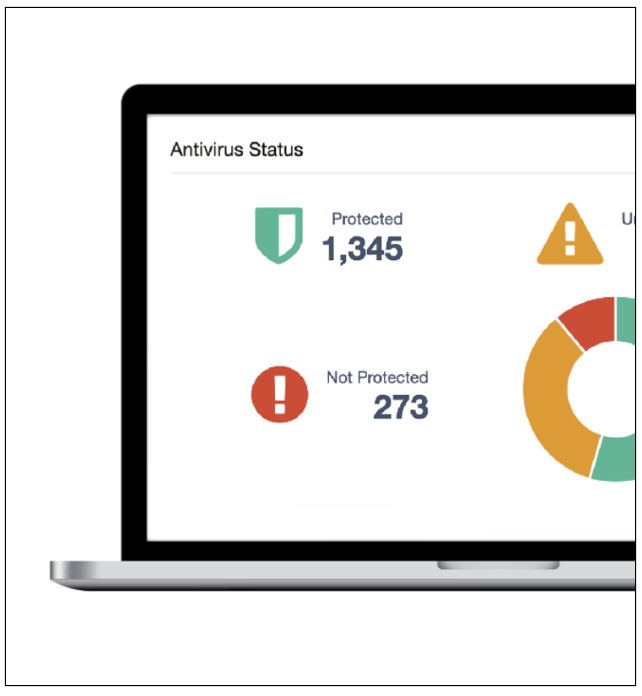
Provided at no additional cost to all Huntress partners, Huntress Managed Antivirus lets MSPs administer Microsoft Defender implementations across all of the customers they support through a multi-tenant interface, rather than rely on the single-tenant console Microsoft provides. New features added to the system since the start of the year include integration with the Huntress ThreatOps team’s incident response workflow that automatically flows detected incidents into the queue for investigation.
“From there, the analysts will take a look and then do an incident report with actionable remediation,” says Dina Bruzek, Huntress’s senior vice president of product and engineering. The vendor can put those remediation measures into effect itself for users as well through its “assisted remediation” feature.
Other features added in recent months include a revised interface with consolidated status views; support for performing bulk actions on one, several, or all of an MSP’s clients; and the ability to receive notifications when endpoints have outdated signature files, haven’t been scanned recently, or are otherwise in an “unhealthy” state. Users who wish to can then automatically enforce compliance with default configurations.
Huntress plans to augment the system’s functionality further on a continuous basis. A new feature set to arrive within the next few weeks, for example, will notify users if integration issues are preventing them from getting alerts in their PSA solution.
According to Bruzek, channel pros are increasingly relying on Microsoft Defender, which is a free component of the Windows operating system, rather than third-party endpoint protection software to keep clients safe. “The efficacy of [Microsoft] Defender has been increasing over the years,” she says. “It’s just as good as if not better than many of the next-gen AV products on the market today, because it leverages all of the intelligence that Windows gets from all of those endpoints.”
The new host isolation functionality Huntress highlighted today lets users automatically or manually separate a breached or infected device from the rest of a customer’s environment. “It’s very important to be able to isolate that host from the network as quickly as you can to prevent lateral movement,” Bruzek notes.
Huntress will then either send an incident report with remediation guidance or perform assisted remediation on the user’s behalf. Users can also isolate all of the endpoints at one customer or every customer they support through the new feature.
The global ThreatOps expansion Huntress announced today adds analysts in the U.K. and Australia to the North American team the company has operated since its founding. According to Bruzek, those new resources, who are on duty overnight and on weekends rather than simply on call, will benefit partners in the U.S. as well as overseas.
“We’re leveraging the ‘follow the sun’ model to be able to provide 24×7 coverage,” she says.
Up next on Huntress’s product roadmap, and due in the first quarter of 2022, is integration between the network-aware EDR solution the vendor acquired in January and the rest of the company’s portfolio.
“That will work with all of the existing workflows that we have today,” Bruzek says. “It will allow us to find malicious processes and be able to provide more information on all the different processes running on the system.”
Bruzek, who joined Huntress late last year after earlier stints at Sourcefire and Cisco, is the company’s first dedicated product chief. “There was no product team other than Kyle and Chris,” she says, referring to CEO Kyle Hanslovan and CTO Chris Bisnett, both of whom are also co-founders. Thanks in part to the $40 million funding round Huntress completed in May, there are now six product managers and 19 developers on staff.
Huntress has also added Director of Product Ed Murphy, Director of R&D Jamie Levy, Head of Threat Operations Center Max Rogers, Chief Marketing Officer Michelle Burtchell, Chief Revenue Officer Mike LaPeters, and Vice President of Partner Success Robert Statsky, among others to its leadership team in recent months.