The rise in ransomware, supply chain attacks, and other malicious hacks underscores the growing need for strong cybersecurity in businesses.
However, even with cutting-edge defenses, human error is a significant weak link. Many business leaders fail to recognize that cybercriminals often use basic tactics to exploit untrained or unaware employees, rather than employing sophisticated software tools or hacks.
Robust cybersecurity measures are essential for thwarting more complex attacks. However, organizations should complement their infrastructure by understanding the most common attack vectors and embracing the “human firewall” philosophy, which highlights employees as the primary defense against cyberattacks.
6 Major Mistakes

Andy Syrewicze
Let’s take a look at the most common mistakes employees make that cyber criminals capitalize on:
- Engaging Phishing Emails and Clicking Suspicious Links: Due to the high volume of emails employees handle daily, spotting phishing attempts becomes challenging, especially as hackers employ advanced AI to enhance their deception. Consequently, untrained employees might fall for phishing emails seeking confidential information or open links leading to malicious software.
- Using outdated software: Hackers are adept at finding and exploiting software vulnerabilities, quickly acting on them before patches are applied. Therefore, prompt installation of software updates is essential. Nonetheless, employees often delay or forget to update their software, jeopardizing organizational security.
- Using weak /overused passwords or not using MFA: Despite the widely recognized risk of weak passwords, many employees still opt for easy-to-remember passwords and reuse them across different services. This practice allows hackers to easily access multiple systems via password stuffing if they crack or obtain a single password. Additionally, multi-factor authentication (MFA) is a MUST in today’s world. Any organization not using an MFA solution is at risk.
- Using unsecured public Wi-Fi: The shift towards remote work has enabled employees to work from almost anywhere, often on unsecured public Wi-Fi networks. This convenience comes at the cost of increased risk, as these networks are more susceptible to hacker intrusions and adversary in the middle (AitM) attacks.
- Not locking computers: It’s common for employees to leave their computers unlocked when stepping away, a habit that poses a risk in both public and office environments. An unlocked workstation can be an open invitation for unauthorized access to sensitive data or for malware installation.
- Sharing devices and credentials: Employees sometimes share their devices or login details with colleagues without considering the risks. Such practices, including leaving devices unattended or exposing login credentials, can provide hackers with easy access to the organization’s digital environment.
The Value of a ‘Human Firewall’
Cybersecurity infrastructure is important, but those measures mean little if employees give cybercriminals easy opportunities to land an attack.
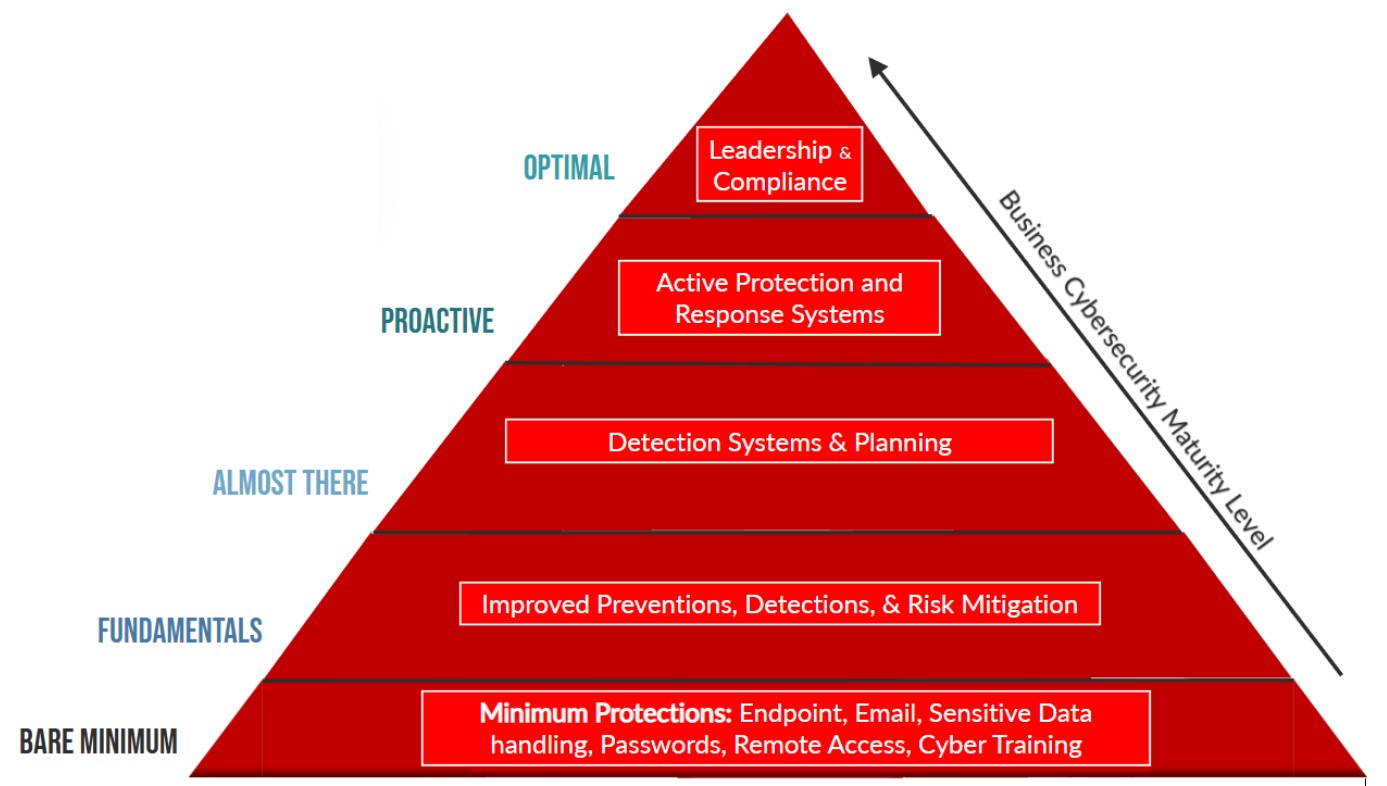
The human firewall philosophy emphasizes employees as the first line of defense against cyberattacks. Organizations can increase the impact of their human firewall by promoting a security-focused culture that aligns with the following triad – with ongoing security awareness training at the heart of this:
- Mindset: Educate employees so they understand the current threat landscape.
- Skillset: Train employees on how to spot attacks and have a plan covering how to address any suspicious activity.
- Toolset: Provide employees with tools to keep their workstations shielded from threats.
Additionally, organizations should insist employees adhere to the following best practices:
- Require the use of complex, unique passwords for all accounts, plus MFA for added security.
- All company devices should be locked and password-protected when not actively in use, both on site and remotely.
- Employees should avoid using unsecure public Wi-Fi. If this can’t be avoided, VPNs or some other connection securing technology should be used.
- Software updates must be installed as soon as they’re available.
- External email addresses should always be reviewed before sending emails.
- Unsolicited emails with links or files attached should be reviewed before opening. Employees should immediately notify IT support when unsure about the safety of attachments.
Employee behavior plays a major part in determining a company’s cybersecurity posture, so reducing the likelihood of human error is important for keeping organizations shielded from the cyber threat landscape.
With the right training, skills and tools, employees can build an effective firewall against cybercriminals and evolving threats.
Andy Syrewicze, security evangelist at Hornetsecurity, is a 20-plus year IT pro specializing in M365, cloud technologies, security, and infrastructure. He holds the Microsoft MVP award in Cloud and Datacenter Management.
Image: DALL-E