IF MANAGED SERVICES were a carnival tent, you might imagine a boisterous MSP in a top hat harkening through a blowhorn at SMB passersby to “step right this way,” inviting them inside to witness with their own eyes the amazing magic of “attack surface management.”
Of course, ASM isn’t snake oil—it is, in fact, a strategic approach to holistic data security. But the term itself is a bit of a marketing-communications innovation. “See it for yourself, folks! The incredible shrinking attack surface!”
The National Institute of Standards and Technology describes the attack surface as the “set of points on the boundary of a system, a system element, or an environment where an attacker can try to enter, cause an effect on, or extract data from, that system, system element, or environment.”
That sounds to many seasoned security experts a lot like the threat landscape we’ve been discussing for a number of decades now. While it may not necessarily be a novel way of thinking, the new(ish) buzzword provides a renewed context for positioning and selling security services to SMB owners and decision makers.
“We’re full of terms, and sometimes I wonder what they actually mean,” quips Oli Thordarson, CEO of Alvaka Networks, an Irvine, Calif.-based MSP with a specialty service in ransomware recovery. “But I see so many IT departments looking to buy the silver bullet,” he says. “And they have no business buying them if they don’t get the basics done, like patching software and the firewall.”

Oli Thordarson
Still, the more MSPs can talk about the “big picture” of security, Thordarson says, the better off everyone will be.
Lawrence Cruciana, president of Charlotte, N.C.-based Corporate Information Technologies, a cybersecurity-focused MSP, agrees. With a long career managing security in highly regulated markets, Cruciana can definitely appreciate a channel jargon joke. “‘Zero trust’ is another great word,” he notes. “There are a lot of vendors that made a lot of money selling zero trust.”
At the end of the day, though, Cruciana concurs with Thordarson that clients need to have a good understanding of their ecosystem as well as the attack surface.
Types Of Attack Surfaces
The attack surface is all-encompassing, but it can be helpful to break all areas of potential attack into categories:
- Technical—Sometimes called the “digital” surface, this refers to the configurations and vulnerability management of the underlying systems.
- Physical—The hardware, office space, server room, etc.
- Social engineering—The people and the information about them and available to them.
These categories have soft, blending boundaries, with their characteristics sometimes overlapping as in a Venn diagram. Network access is a good example. A user’s login (social engineering) may enable access to a certain area, but it’s important to think about the limits within the network that that login should provide (technical).
The term “zero trust” is born of this interdependent relationship among attack surface types. “‘Conditional access’ was once the buzzword,” Cruciana says. “But, essentially, it means letting people do what they need to do—and defining when and where that might be—without being overly permissive.”
ASM 101
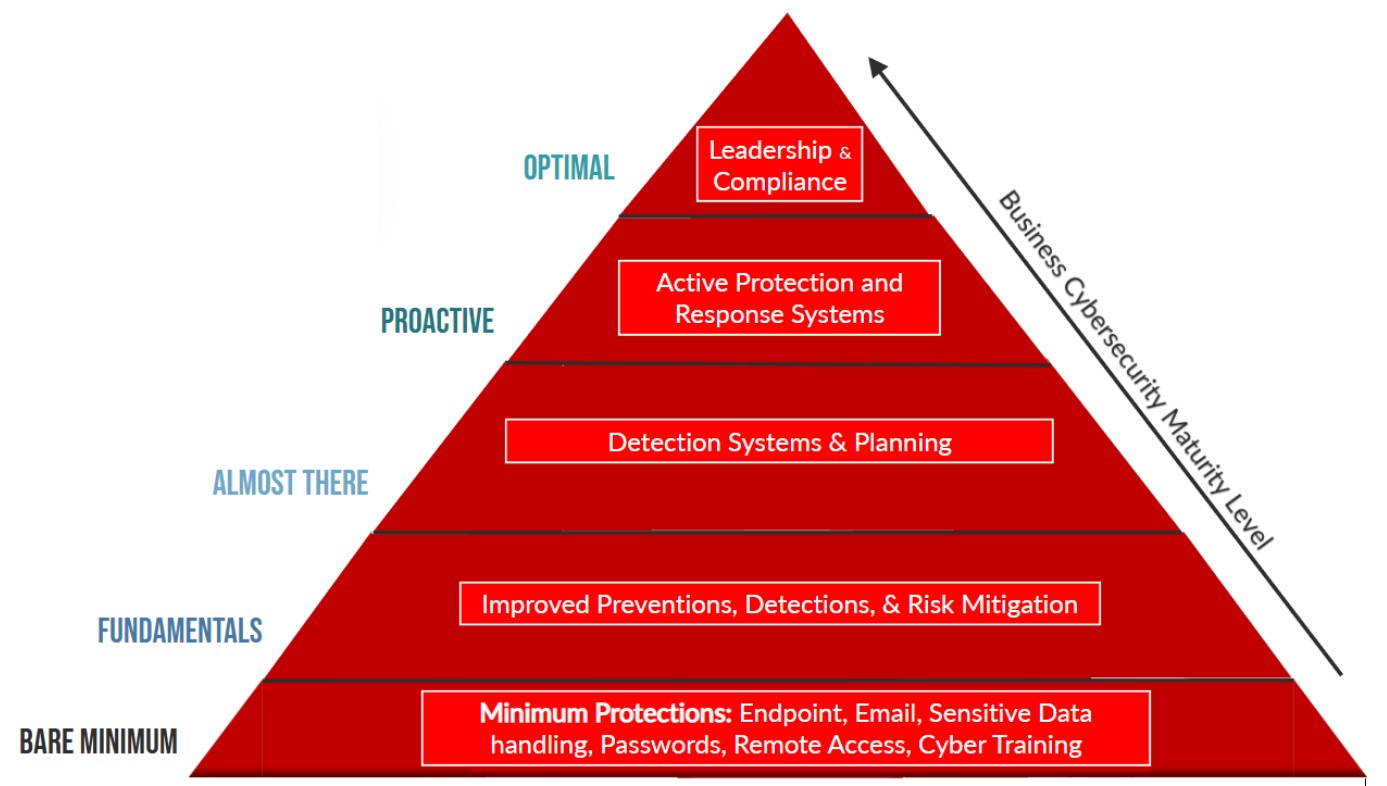
For many SMBs, the attack surface can feel like a sprawling void of overwhelming endlessness. This is where the MSP can be the voice of reason in helping them to shrink that threat.
“In the MSP and security space, we’re in the business of surprise elimination,” says Cruciana. “We can be proactive in eliminating surprises by understanding and thinking about the entire attack surface.”
Cruciana starts with clients by mapping out their ecosystems. “This early stage recon is so critical to be able to inform what attack might be successful,” he says. This involves working with SMBs to “understand all the constituent components on the inside and any way for an adversary to get a foothold on the inside of a network.” Vulnerabilities include overly permissive accounts, certain third-party access, remote sessions, file sharing, etc.
“You often find that the attack surface is way bigger than they ever dreamed of,” he says, “and rife with possibilities for exploitation.”
Next, Cruciana helps his clients understand the social engineering areas of the attack surface. This includes employees and their behaviors as well as corporate communications. For example, “What info do you publish about your company?” he asks.
He suggests that clients “think like an attacker. Inform yourself about how they think in the social space.”

Lawrence Cruciana
From here, Cruciana helps SMBs take their first steps. He advises them to start with where they think their greatest vulnerabilities are. “Is it your low sophistication of standards? Then, maybe it’s the technical attack surface where you begin. Is it a company culture that doesn’t value security? Then, maybe it’s social where you need to start. Maybe you have a billion subvendors, and it’s the ecosystem that needs addressing first.”
Cruciana advises SMBs to “just start somewhere” and make incremental improvements. Too often, he says, he sees clients who have paralyzed themselves with “so many choices, you don’t know what to pick.”
Thordarson, for his part, suggests starting with the lowest-hanging fruit. “Most breaches come when someone missed something in the basics,” he says. “Taking away admin credentials and using least privilege doesn’t cost anything. With least privilege, they only have traditional user rights and can’t really have privileges to load software and things like that. Bad guys are going to be extremely hampered.”
“The most vulnerable attack surfaces are the unpatched PCs and unpatched servers,” Thordarson says. He ensures that his clients address unpatched firewalls and user PCs without multifactor authentication and which the users have administrator level login.
Unpatched Exchange servers are, in particular, “a big deal,” he says. “It has slowed down a lot in the last year, but the pandemic totally opened up rich fields of harvest for hackers and they’re still working those. IT staff everywhere had to rush to get everyone working from home, and it created a field day for the hackers.”
In a single breath, Thordarson lists the ASM basics: “So many attacks could be mitigated if companies patch their software, keep physical devices [like firewalls] up to date and give users least-privilege access [instead of an admin credential] and have multifactor authentication. Just those things, along with network segmentation and EDR [endpoint detection and response] and XDR [extended detection and response], and there’s your 2023 primer right there.”
ASM 201
For the alchemy of attack surface management to yield true results, MSPs are going to have to establish standards and best practices for their SMB clients.
Once the client’s ecosystem has been mapped out and social vulnerabilities identified, ASM basics such as MFA, least-privilege access, and patching will need to be double-checked.
Next on the ASM list is network segmentation, including the use of such tools as EDR/XDR, digital identity management, whitelisting, ring fencing, etc. “Data mapping is the sibling to network segmentation,” Thordarson explains. “What data do you have, and where does it reside? You need to know this so you can properly protect your network.”
He notes that “ring fencing is the same thing as network segmentation. “It’s a good way to reduce the risk because it limits what can be seen and accessed by hackers. Once you can break in the front door, you can walk around anywhere you want.”
But there’s a caveat, he adds. “If every room has a lock and card key access, you’re going to have a hard time getting around.”
Thordarson uses the example of grocery store items that, once upon a time, were available to consumers on the open shelves but are now behind the counter or in a locked cabinet. Think razor blades, pseudoephedrine, or even baby formula. “Prized goods in the physical world are segmented off,” he says. “So, you have to know where your vulnerable data is and have levels of protection for that.”
He continues, “Implementing endpoint detection and response would mitigate the threat to an attack surface. You don’t want to have a hard outer shell and soft, chewy inside. You need protections inside. Once they crack through the outer shell of the ‘Tootsie Pop,’ they need to be tracked.”
The MSP will want to log what was extricated to see if an attacker didn’t really go anywhere—or whether they got anything important. “If the network is broken into and you’re doing a forensics study, you’ll need to know where data is and what was taken.”
From there, MSPs could conceivably get even fancier in their ASM techniques. Cruciana, for example, is a proponent of a “deception framework.” By altering the way certain hardware and software appear, he explains, bad actors doing reconnaissance for a potential hack job may “overlook a commonly understood vulnerability.”
He explains, “It’s the act of simply modifying some of the attributes to evoke a different set of attacks or TTPs [tactics, techniques, and procedures] that hackers take.”
Tools and Learning
To help SMB clients get their minds—and strategies—in line with attack surface management, Cruciana encourages them to learn more. Some of his favorite mentoring tools, toys, and references include:
- The cyber kill chain—Developed originally by Lockheed Martin for the U.S. Military, this model outlines seven sequential steps that cyberattacks will take. Knowing these steps will help clients understand the ways in which their security protocols may thwart or mitigate attacks throughout the process. Cruciana says a simple search will produce results outlining this concept.
- Network scanning tools—At a minimum, networks should be monitored for certain characteristics. A decent scanning tool should also enable A/B scans to detect differences. While many MSPs may be using more sophisticated alternatives, Cruciana notes that Nmap is a solid free option.
- Database vulnerability scanners—There are many A/B attack surface analyzers, Cruciana says. “But the SCUBA tool is easy and free and will analyze your Azure configuration. The documentation is written by humans in an understandable way. It lets you establish a baseline and compare your results to what’s known to be good.”
- Company awareness campaigns—A good, old-fashioned ongoing training effort will help establish a company-wide culture that’s security minded. “Phishing training is old hat at this point, but it works,” Cruciana says. “Think like an attacker and help employees think about how they behave.” MSPs should also tell clients to look at what’s being shared publicly on their blogs and social media, he adds.
- Shodan search engine—Dubbed the “search engine for the Internet of Things,” Shodan is used primarily by hackers and security professionals alike to map and gather information about the network. Cruciana points to this website as a reason why deception is employed. “This is a search engine for system attributes,” he explains. “Anyone can see all the Windows servers that are running, and that a certain version runs a certain patch with a vulnerability.”
- Darknet Diaries—This is a popular mainstream podcast that tells “true stories from the dark side of the Internet” about hackers, cybercrimes, ransomware, and more. Cruciana is a big fan and says he shares some of the stories with clients.
A Community of Continuous Discovery
Attack surface management is much more than a marketing buzzword. It’s a holistic approach to security that does not stop or end with an SMB’s network. In fact, it doesn’t stop with the SMB at all.
For Cruciana, a community-minded approach to minimizing the attack surface is needed. And this must include software developers, who may overlook the effect of things like documentation.
“We need an understanding that the metadata [of release notes] exposes on the network all those things that have changed,” he says, including “the signature and detection of the application.” This, in turn, can affect the attack surface “almost as much as default security permissions,” he says.
“Every time you make a change to a system, you have to make that analysis,” Cruciana stresses. “We’re solving for systemic risk. Attack surface management is continuous discovery and analysis.”
Thordarson agrees. “We’re constantly educating and advising companies to be more secure,” he says. “And the bigger the systems, the more there is to try to protect. If you get into hundreds or thousands of users, it’s harder to protect that stuff. We’re all still learning a ton about security and what’s important.”
Image: iStock