The explosive rise in ransomware attacks is increasingly being thought of as a pandemic of its own.
Earlier this year, the Biden administration released an official statement urging private sectors to take immediate action on shoring up their defenses against potential cyberthreats. This is the latest and most urgent warning provided yet, following a series of regular reminders since the fall of 2021 to implement robust cybersecurity measures. The statement further prompts companies to act quickly and rely on cyber resources provided by the federal government.
And while there has been no actionable intelligence on any impending or dramatic increases in malicious activity as the Russian invasion of Ukraine continues, following actionable cyber best practices will help protect you and your clients’ businesses and keep the cyberattack surface to a minimum in the face of all kinds of rising threats.
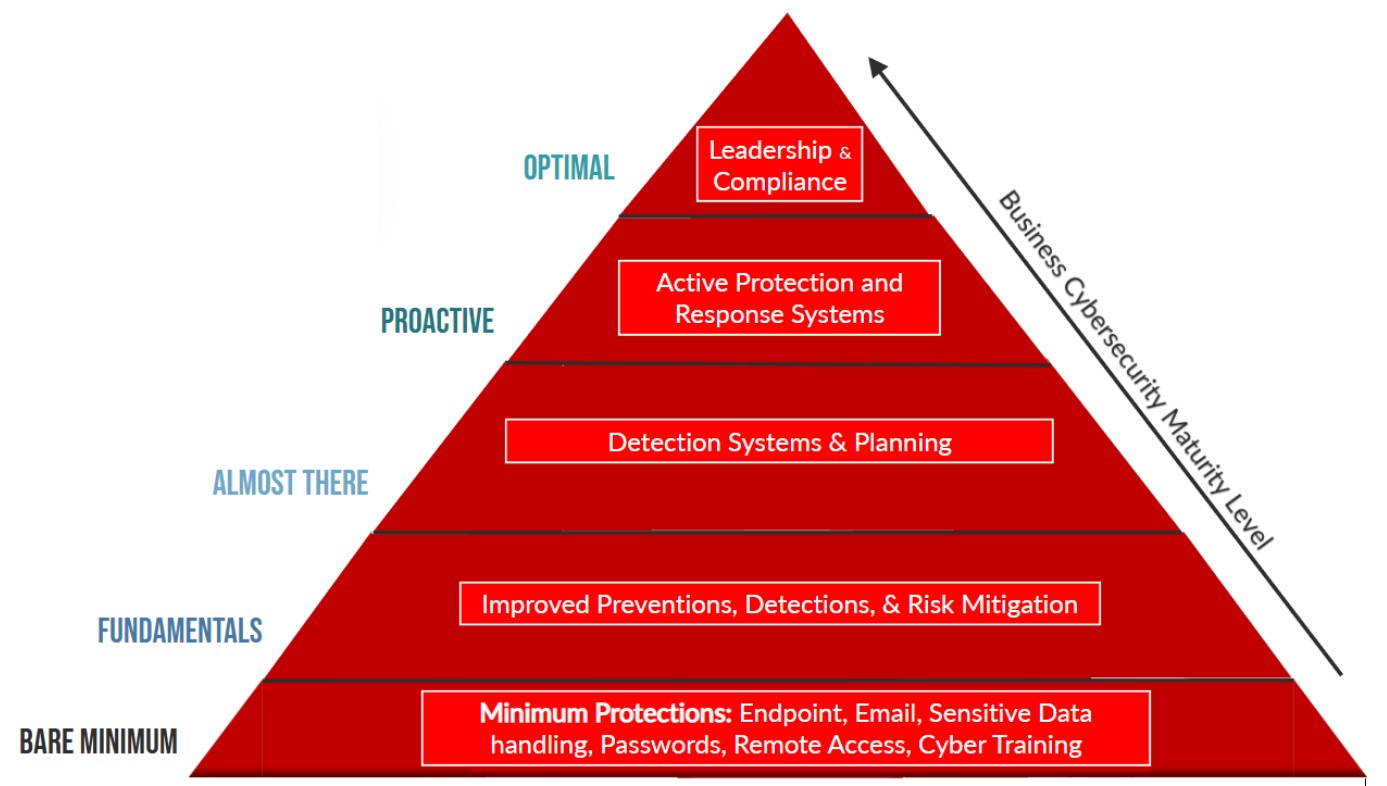
How to Improve Your Cybersecurity Posture
Below is a list of five effective best practices that you and your clients can undertake to safeguard against ransomware attacks.
1. Security Awareness and Training
Whether or not your client has a dedicated IT security team, they still rely on your ongoing support and expertise. As an MSP, educating your clients on key IT best practices allows them to better understand and embrace their responsibility for cybersecurity across their organization. Security is the responsibility of everyone, and fostering general awareness is the first line of defense. Clients who are aware of their role in maintaining IT security can better protect their business in the long term.
2. Establish and Follow IT Best Practices
Adopting best practices for your own business as well as your clients’ ensures you are set for long-term success and continue to operate effectively. The key element to best practices is consistency. This is especially true for the IT world as even one breach could be detrimental to operations.
Some examples of best practices include:
- Implementing backup and disaster recovery (BDR) processes and having an incident response plan
- Having organizational support and buy-in on patching and upgrade activities, particularly for firewall and VPN appliances
- Upkeeping an effective employee management process, including having a standard offboarding process and monitoring/auditing user access rights regularly
- Establishing app-based multifactor authentication (MFA/2FA) setup for all applications and RMM tools
- Removing internet-exposed Remote Desktop Protocol (RDP) services
- Requiring complex passwords
- Learning how to identify phishing emails and social engineering attacks
3. Implement an Effective Security Stack with Active Monitoring
There is no doubt that building and maintaining a security stack is one of your most important tasks. It can also be quite an exercise in balance—employing many diverse cybersecurity tools means your clients’ systems are protected, but add too many and the stack becomes complex and unmanageable. This can easily lead to oversight and vulnerabilities, not to mention a large up-front investment for the technology. An elegant security stack will include up-to-date endpoint protection technology, backup and recovery technology, MFA capability, VPN or zero-trust remote network access, vulnerability management with patching, and 24/7 monitoring with active response.
4. Backups
To ensure business continuity in the event of a disaster or emergency, backups are critical. Adding backups to your cybersecurity toolkit can also help prevent disruption during a cyberattack. By storing critical data in offline backups, cloud backups, or on external hard drives/storage devices that cannot be accessed from a potentially compromised network, your clients can safely access their data with little to no interruptions to operations—even if a malicious actor has encrypted sensitive data and is holding it hostage. It’s important that backup data is not accessible for modification or deletion from the primary network.
5. Immediate Incident Response – Adopting an ‘Assume Breach’ Posture
As threat actors continue to evolve and employ new tools and techniques, you’ll need to establish an efficient incident response system—and help clients do the same. During an attack, response time is crucial and often determines whether the malicious group succeeds in compromising systems and encrypting information. Attackers are moving faster than ever and the window of time between an initial breach and ransomware deployment is shrinking. Investing in an around-the-clock detection and response service means that you can fight back within minutes. It’s no longer an option to wait hours or days to detect and respond to suspicious network activity.
JON MURCHISON, founder and CEO of Blackpoint Cyber, started his career in network engineering and IT operations but quickly made the switch over to the covert world of the intelligence community. He has since spent more than 12 years planning, conducting, and executing high-priority national security missions. As a former NSA computer operations expert and IT professional, he brings a unique perspective to the mission of developing cyber defense software that effectively detects and detains purposeful cyber intrusions and insider threats.