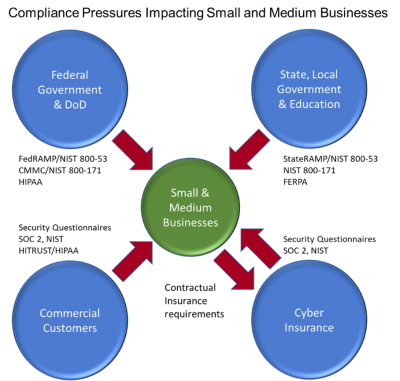
The surge in public cybersecurity breaches is continuing to drive companies into proactive and comprehensive approaches to reducing cybersecurity risk. The waves of attention and consequences are moving beyond large organizations to small and medium ones, including government and commercial businesses.
If you’re seeing increasing demands in the form of cybersecurity questionnaires or compliance requirements, you’re likely falling prey to “cascading compliance requirements.” Add StateRAMP to the widening array of cybersecurity and compliance requirements impacting companies of all sizes.
These cascading compliance requirements are usually coming as part of your client’s vendor/supplier selection process. As enterprises operationalize their vendor and third-party management program, they use questionnaires and security requirements to understand the risk that a vendor poses to their business. And this wave is not slowing down, but is growing, as government and cyber insurance companies are requiring cybersecurity programs from their suppliers or clients too.
As supplier scrutiny increases, we’re seeing requirements for specific frameworks and certifications such as SOC 2, ISO 27001, and NIST compliance. It is increasingly the case that SMBs must secure a SOC 2 Type 2 or similar attestations/certifications or lose eligibility to win or sustain business with their enterprise prospects.
State and local governments are joining the mix of organizations compelling small and medium businesses to address their cybersecurity risk via compliance initiatives.
 StateRAMP, among the newest security requirements, follows in the footsteps of the more broadly deployed FedRAMP certification, which many software and cloud-based service providers must implement to be eligible for federal contracts.
StateRAMP, among the newest security requirements, follows in the footsteps of the more broadly deployed FedRAMP certification, which many software and cloud-based service providers must implement to be eligible for federal contracts.
StateRAMP is a set of security controls and oversight mandates for suppliers to state and local governments, including educational institutions. Arizona and Texas have taken the lead among at least a half-dozen other states developing StateRAMP certification.
Arizona’s AZRAMP program debuted in 2021 and is progressing to the broader-based StateRAMP requirements. All the security controls are based on NIST 800-53, which is the same underlying standard for FedRAMP. Here are some of the AZRAMP requirements software and cloud providers must demonstrate:
- Meet 35 basic controls to bid on Arizona state projects or protect their data
- Meet 125 basic controls to protect public data
- Meet 325 basic controls to protect sensitive data
Currently, over 235 active vendors meet AZRAMP standards. The supply base will be required to shift to StateRAMP, which provides a more formal process for validating compliance.
Texas has pushed ahead even more aggressively. It passed the TX-RAMP legislation in the summer of 2021, and required all SaaS, IaaS, and PaaS vendors to be TX-RAMP authorized by January 2022. Authorization is an interim step to certification, which will be required within 18 months thereafter. Compliance is mandated before suppliers can renew or secure contracts with state agencies or higher education and public community colleges. As with the Arizona-based program, TX-RAMP is the state-specific version of what is presumably the multi-state standard, StateRAMP. It’s unclear at the time of this article to what degree states will reciprocate among the state-specific standards, but all states signing on for StateRAMP will be aligned on a common reciprocal standard.
As StateRAMP develops and is deployed across multiple states, an important consideration is that StateRAMP is reciprocal with FedRAMP certification. That means companies that achieve FedRAMP will see expedited authorization as suppliers at the state, local, and educational level. Unfortunately, currently you will not immediately get FedRAMP Authorization to Operate (ATO) based solely on StateRAMP. However, the effort in either case will substantially lower the lift for companies that operate at both the state and federal level.
The strategy of using FedRAMP in lieu of state-level certifications or StateRAMP itself has a particular challenge. To pursue FedRAMP, a company needs to have a federal agency sponsor. Of course, this is part of the solution that StateRAMP solves.
The Texas legislation provides some guidance on how StateRAMP aligns with FedRAMP. TX-RAMP identifies two certification levels:
- Level 1 for public/nonconfidential information or low-impact systems. Level 1 certification roughly maps to FedRAMP Low authorization.
- Level 2 for confidential/regulated data in moderate- or high-impact systems, which roughly maps to FedRAMP Moderate authorization.
As TX-RAMP roles out, over 200 products have been authorized via either provisional status. They now have a window of up to 18 months to receive their full TX-RAMP certification. Provisional status requires sponsorship from an existing agency relationship attesting to a previously conducted assessment, or a third-party assessment made available for review by regulators. Another 250 products are authorized via TX-RAMP certification or “Existing Other RAMP-Certification” (reciprocal FedRAMP certification).
TX-RAMP’s 18-month provisional window illustrates the stakes for companies seeking to retain or secure business with state and local government. In our experience, FedRAMP typically takes at least 12-18 months to secure certification. Thus, the 18-month window leaves vendors little time to spare if they are not well into developing a formal information security program.
Sustaining StateRAMP or FedRAMP certification requires an ongoing commitment to security. The underlying controls require continuous monitoring and due diligence. You should expect this level of security operations to necessitate hiring qualified security professionals, or outsourcing your security operations to qualified firms.
Many companies will see the growing compliance and security scrutiny as a significant financial and operational burden. Indeed, the investment of time and money is not insignificant. However, in our experience, there’s a countervailing benefit to that burden. Once you’ve achieved a recognized security certification, you’ll find it to be a competitive advantage, including:
- The ability to participate in an exclusive community of providers who have proven their commitment and capability in cybersecurity
- A barrier to entry from other competitors
- A valuable marketing tool
- Reduced “revenue friction” as your security questionnaire and compliance responses are more favorable and readily available
SMBs may choose to dismiss or accept the risk of cybersecurity breaches on their own behalf, but they are finding it increasingly difficult to do so if they supply products to larger organizations, whether commercial or government. This trend is not going to stop, because public breaches and ransomware continue to drive visibility and pressure on organizations of all sizes.
These will drive your customers to cascade their requirements onto you, and you to drive your requirements onto your suppliers. Companies that embrace the security-first perspective, and leverage the market advantages, will both reduce risk and capture opportunity.
MARK KIRSTEIN, CISSP, is vice president of customer success at Cosant Cyber Security.