AFTER MORE THAN 20 YEARS, the basics of Mac management have fundamentally changed. Advanced security features of macOS on Macs with Apple’s M1, M2 (pictured below), and T2 chips have made obsolete the key management methods that Mac IT administrators have relied on for years.
Today, the operating system boots and runs from a read-only image of macOS, installed from a read-only volume that can only be modified by the Apple software update process. This means that every instance of any given version of macOS is installed and running precisely as written by Apple.
macOS System Integrity Protection (SIP) safeguards the computer by preventing execution of unauthorized software.
Apps downloaded from the App Store are automatically authorized to install and run. Apps that a developer notarizes and distributes directly to users are also authorized. Unauthorized apps may be launched after manually configuring a security exception.
Let’s take a look at how things have changed.
Clone Copies
Then: On a scheduled basis, Mac admins would make a bootable “clone” copy of an active system at least once a day. Clone copies could be useful for troubleshooting, and as an aspect of a backup plan.
N ow: Admins still make clone copies containing all files and settings, but not the operating system. The macOS resides on a write-protected volume that’s separate from the data volume where all other files reside, including settings and extensions.
ow: Admins still make clone copies containing all files and settings, but not the operating system. The macOS resides on a write-protected volume that’s separate from the data volume where all other files reside, including settings and extensions.
Which means: Restoring a system to a bootable state from a clone copy has become a two-step process: First the operating system is installed on the new volume, then the data is migrated from the clone to the new volume using Apple Migration Assistant.
Important Fact: Internal storage of an Apple M1 or M2 Mac computer is linked uniquely to the computer hardware in which it is installed. Storage from one computer cannot be removed and used with any another computer.
Backup and restore are essential.
Rules of SIP
SIP restricts components of the file system to read-only in specific critical locations to help prevent malicious code from modifying them. With an Intel-based Mac, disabling SIP removes protection for all partitions on the physical storage device and process running on the system, regardless of whether the code is running sandboxed or with administrative privileges.
Single-User Mode is a good example of a feature no longer supported because it violates the rules of SIP. A Mac booted into Single-User Mode exposes the system kernel and file system to potential modification from the terminal console as super user.
Then: Using Disk Utility, Mac admins would make an image copy of a volume containing the operating system and data. A disk image might be used to restore a computer to a bootable state after replacing or erasing a hard drive, or for reference when troubleshooting. A prudent administrator would typically make offline clone and image copies of a disk, prior to making significant changes to a system.
Now: The Disk Utility User Guide for Mac states, “You can’t create images of individual APFS [Apple File System] volumes. You can’t create images of APFS containers on Mac computers with Apple silicon or an Apple T2 Security Chip.”
Which Means: The disk image feature exists today for making disk images of groups of files and folders, but not APFS volumes or containers.
Important Fact: If the storage in your M1 Mac has failed, the computer won’t boot. If the computer has failed, the storage becomes inaccessible.
Backup and restore are essential.
Mobile Device Management
The flexibility of the Apple security framework built into every Apple device enables organizations of any size to easily design and apply configuration templates via mobile device management (MDM) for securely managing both personal and business applications and data on a single device. Securing both personal and corporate apps and data are equally important in the Apple framework. To simplify regulatory compliance, some MDM platforms include security management controls mapped directly to recognized NIST, HIPAA, PCI, and other security frameworks.
Using Apple Business Manager in conjunction with an MDM platform, Macs and application software are deployed, managed, and secured using policy templates to configure various features and settings.
Apple Business Manager supports federated authentication using both Google Workspace and Microsoft Azure Active Directory, which automatically sets up Managed Apple IDs in Apple Business Manager when users log in with their Google Workspace or Azure AD user credentials.
Recently, Apple began offering its own MDM called Apple Business Essentials (pictured below), which is a subscription service intended to be paired with AppleCare+ support to provide device management, 24/7 software support, and cloud storage for the small office.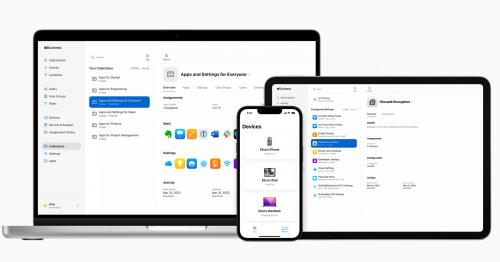
Then: Target Disk Mode, enabled at bootup by invoking a keyboard command, enabled a computer to function as a hard drive that could be connected to another Mac for troubleshooting and repair, imaging and cloning, or even to boot another computer.
Now: Apple M1 and M2 Macs can boot into Shared Disk Mode, which in many ways is functionally equivalent to Target Disk Mode. Computers in Target Disk Mode and Shared Disk Mode can be connected to another computer as a hard drive for the purpose of copying files directly between computers. This could be very useful for quickly copying a large volume of data.
Which Means: Admins can no longer troubleshoot hardware and software issues by testing the ability of a system in Target Disk Mode to boot another similar Mac.
Erase All Content
macOS Monterey recently added a feature that makes it easy to quickly erase everything from the Mac except the operating system. Good news? Bad news? Got a backup? Introduction of this feature further aligns macOS with the iPadOS and iOS feature set. The Erase All Content feature is useful for immediately and securely removing all user data from a managed device, but also potentially dangerous.
Users of macOS Monterey will find the new feature under the System Preferences menu. Use this feature wisely since there’s not a way to undo Erase All Content.
One last time, in case you missed the emphasis: Backup and restore are essential.
What Remains
It’s clear that many basics of Mac administration and management are fundamentally changed or have even been eliminated. Don’t expect to boot a new Apple silicon Mac using a flash drive containing current versions of your favorite repair utilities. Also gone are the days of wondering whether the operating system or system volume are corrupt. System software is installed from an immutable volume, which can only be modified by Apple Software Update. Your new M1 or M2 Mac can’t boot or run from an unverified or corrupted copy of macOS.
 Many essential management strategies and tactics endure, however, such as multi-destination data backup, verification and test restore of backup files, securing the network environment and endpoints, and internet connection hardening and redundancy. It seems that the more things change, the more things remain the same.
Many essential management strategies and tactics endure, however, such as multi-destination data backup, verification and test restore of backup files, securing the network environment and endpoints, and internet connection hardening and redundancy. It seems that the more things change, the more things remain the same.
TIM MALM is the owner of CorePoint360. He has specialized in support for the Mac in a network environment since the early ’90s.
Images courtesy of Apple