I COULD NOT HAVE BEGUN TO REALIZE just how pertinent this topic would be when I first planned these articles, but here we are. When disasters like the coronavirus pandemic strike, we must enable our clients to stay working against the odds; maintaining their security even as we open their networks to new threats posed by their personal PCs. That means securing the target and remote machines, and the connectivity itself. And it must be done on a reasonable budget, implemented as quickly and easily as possible, with minimal support burden down the road.
Securing the Target Machines
Managed service providers are typically securing managed endpoints, which should include every desktop at every site for all of us. But there are some additional challenges once we start providing nearly ubiquitous remote access to our users. When the remote machines (usually, Windows or Mac laptops) were all under our management, there was a reasonable assumption that they were “”sanitary”” and generally well protected. But we are not living that reality any longer; suddenly we are supporting many unknowns at once. This makes securing the managed targets both more difficult and more critical. Most of us are already doing automated patching, endpoint detection and response (EDR) or some sort of advanced AV, DNS filtering, and more, but let’s talk about that “”more.””
We rely upon CylancePROTECT and CylanceOPTICS through Solutions Granted for our EDR solution and for the vendor’s support and management of those endpoints. Solutions Granted offers three tiers of services with its endpoint offerings. Net Sciences has recently moved to the third tier, which provides 24/7 SOC services for those endpoints, as well as Infocyte’s advanced threat detection and incident response (known as the “”Response Ready”” program). This allows Solutions Granted even greater visibility into the endpoints, enabling the provider to both track malicious activity and, if need be, isolate it entirely from its network, locking down connectivity from the machine to only its SOC. This is just the sort of extra protection we needed and is a great “”force multiplier”” that we could not even approximate on our own.
Securing the Remote Machines
We are now in a truly different world when it comes to providing remote access to our clients. As recently as February, we did not have a single remote endpoint connecting to our networks that was unmanaged. For many of us, that has changed in the past month, with hundreds of new, potentially dangerous connections set up with almost no “”endpoint vetting”” done.
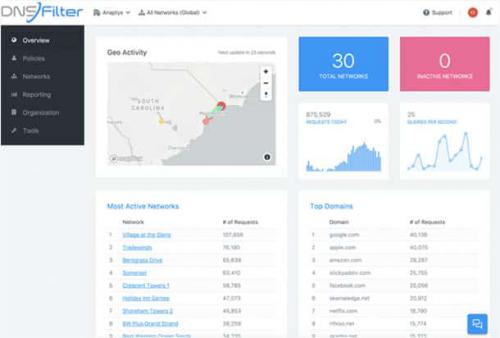
To mitigate this issue, we have decided to limit collateral damage by using DNS filtering on these new endpoints. As much as we’d like to do full EDR, there are problems of cost and support limiting us. As anyone in this business knows, when you work on any machine, whatever next goes wrong, you “”own it.”” You could set a screen saver, and months later, when the 10-year-old hard drive dies, they will know it was your fault.
Therefore, whatever we do to secure these endpoints, it must be all but invisible to the user. We’ve partnered with DNSFilter and use its agents, which can be silently installed. The agents filter web traffic, of course, but in some cases can prevent keystroke logging or other compromises from “”phoning home.”” It’s a small but important step that’s safe and helps our clients and us.
Securing the Connection
In the old days (last year), I depended upon SSL VPN software clients to secure these connections. Larger sites had remote access appliances that provided more capability, including “”endpoint vetting”” and clientless connectivity by means of sophisticated VPN portals, while also reducing CPU and memory load from the firewall. But SSL VPN had its own issues, including the need to work to secure the connection (such as limiting “”lateral movement”” inside the target network, and more). SSL VPN also doesn’t include integrated, full-featured multifactor authentication (MFA) that most of us consider baseline nowadays. SSL VPN connectivity remains an important arrow in the remote access quiver, but it wasn’t right for this sudden need.
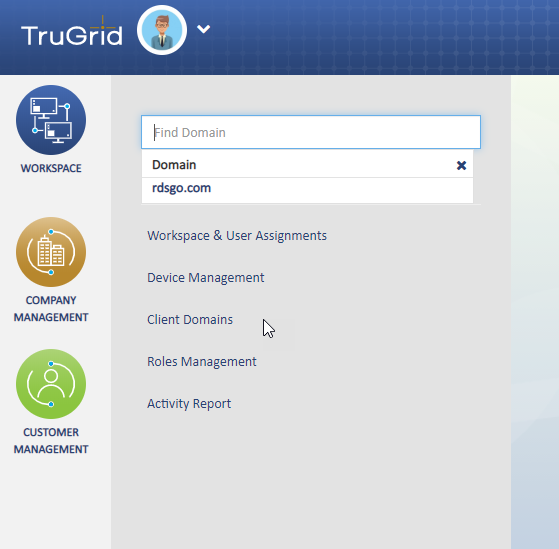
This is where proxied Microsoft Remote Desktop (RDS) connectivity comes in. While an RDS gateway offers a quick and dirty answer, it doesn’t check all the security and management boxes; there are also concerns about management, privacy on the target machines, and more, so the search continued. When I found TruGrid SecureRDP, I was intrigued. It seemed too good to be true, but within hours of use, I was sold. And as interest in remote connectivity ticked up and I realized just how dramatically our clients’ needs were going to increase, I dove in, much more quickly than I normally would.
We don’t have the space to review the solution in depth, but to briefly summarize, you can think of it as an enhanced RDS client, working through a hosted and secured web proxy. It is delivered by means of either a browser plugin or a “”connector”” client installed on the remote machine. On the back end, you install TruGrid’s Sentry application, which is an Active Directory connector. Next, you create a security group to enumerate users who should be granted remote access. In TruGrid’s hosting space you create the target machines that are to be accessed remotely, and then designate whom has access to which machine(s). Additionally, you have access to statistics on who connects from where and when to what, and a bit more.
There is more to like, such as the ability to fine-tune hosting sites, “”direct connect”” options, integrated MFA with push capabilities (if you use TruGrid’s iOS or Android app), and more. And since this is all based on RDP/RDS, you can also control the connection by group policy, limiting drive, printer and other resource remapping, and more; and managing your data leak prevention risk. Once you’re good at it, you can expect a 20-minute server install, 20 minutes in TruGrid’s cloud, and 10 to 20 minutes per remote machine. That remote install is simple enough that many users can do it on their own. But nothing is perfect and there were some early authentication issues, but they were addressed quickly, right in the midst of our March COVID-19 madness.
Further Down the Road
In the short term, DNSFilter agents and secure, proxied access from TruGrid are a great start on securing the new endpoints we now support. Longer term, our goal is to completely secure these new endpoints to the level of our fully managed ones. They will not be sitting behind UTM firewalls any time soon, but we can apply the rest of our stack to them, including RMM agents, patch management, EDR clients and SOC services, dark web alerting, and user training.
 Perhaps a more secure remote workforce will be the new normal and a silver lining to this amazing challenge we are all facing.
Perhaps a more secure remote workforce will be the new normal and a silver lining to this amazing challenge we are all facing.
JOSHUA LIBERMAN is president of Net Sciences, founded in 1996. A 25-year ASCII Group member, former rock climber and martial artist, and lifelong photographer, Liberman has visited five continents and speaks many languages. He also writes and speaks in the IT field and raises Siberian Huskies with his wife Heidi, who calls him the Most Interesting Geek in the World.
Opening image: Courtesy of TruGrid